2021 Gartner® Hype Cycle™ for Security Operations
What is the 2021 Gartner Hype Cycle for Security Operations?
As new technologies emerge and make bold claims, it gets harder for organizations to make risk-based decisions about what security operations technologies meet their business objectives and needs.
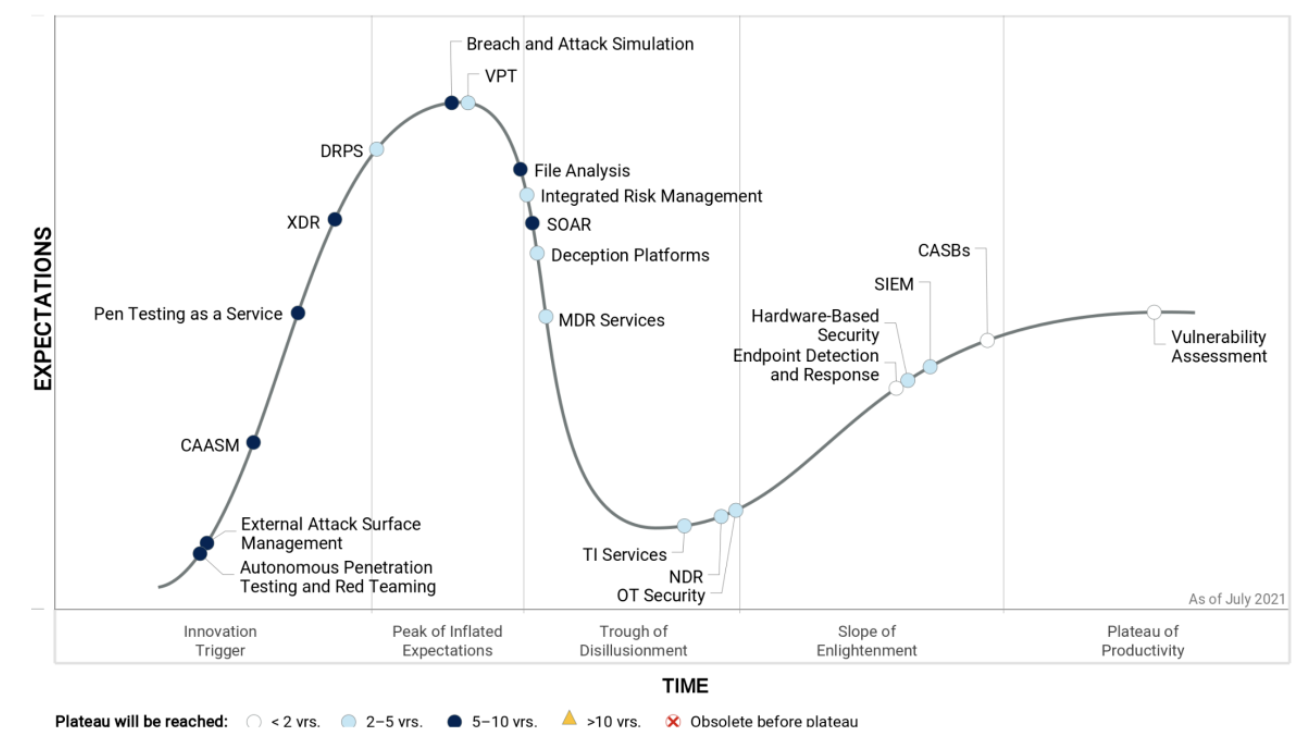
Gartner Hype Cycles provide a graphic representation of the maturity and adoption of technologies and applications, and how they are potentially relevant to solving real business problems and exploiting new opportunities.
Hype Cycle for Security Operations, 2021
Source:https://www.gartner.com/en/research/methodologies/gartner-hype-cycle
Check our latest Gartner Blog: Implement a Continuous Threat Exposure Management (CTEM) Program
Breach and Attack Simulation (BAS) Technologies
According to Gartner, "technologically, the security domain has continued to be siloed, with much focus being directed toward specific domains, such as network detection and response (NDR) and operational technology (OT) security. At the same time, capabilities such as Breach and Attack Simulation (BAS) join domains together, providing visibility and verification of that visibility, as well as response planning and effective response testing."
In the 2021 Hype Cycle for Security Operations, Gartner highlights BAS as the peak of inflated expectations and defines the impact of BAS technologies as: “BAS allows organizations to automate and run continuous security assessments that evaluate and assess a larger percentage of an organization’s assets and on a more frequent basis. BAS continually adds new threats and expands the scope and depth of its capabilities."
In this report, Gartner emphasizes:
Since it is not able to be ready for every possible threat, security leaders need to adopt business-driven decisions for their security operations technologies.
Security leaders must make decisions about security operations technologies by evaluating how to manage risk to their organizations.
One of the major requirements for the security operations personnel is having modern technologies that provide fast detection and mitigation of threats within reducing exposure.
Before investing in security operations services and capabilities, organizations need to adjust their priorities to meet the changes in IT and the threat landscape.
By focusing on risks, organizations can cut through the noise in security and provide transformational benefits.
In addition, Gartner underlines that "Security and risk management leaders responsible for security operations should be looking to reduce overlapping capability across different technologies and become more risk-focused."
Check our latest Gartner Blog: Implement a Continuous Threat Exposure Management (CTEM) Program
![]()
Gartner, Hype Cycle for Security Operations 2021, 29 June 2022, Mitchell Schneider, John Collins, Craig Lawson, Jeremy D'Hoinne
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Gartner and Hype Cycle are registered trademarks and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.











