Continuous Threat Exposure Management
In today’s evolving threat landscape, proactive security is essential. CTEM helps you stay ahead by continuously identifying, validating, and remediating exposures before attackers exploit them.
What is Continuous Threat Exposure Management (CTEM)
CTEM is a continuous, risk-centric approach that empowers security teams to identify, validate, and remediate exposures before adversaries exploit them. It goes beyond static vulnerability lists by simulating real-world attack paths and measuring how effectively your controls protect critical assets across your environment. By doing so, CTEM enables more confident decisions and stronger operational resilience.
Core Components of an Effective CTEM Solution
-
Prioritize exploitable risks, not just CVEs
-
Reveal hidden attack paths across enterprise environment
-
Strengthen defenses for critical assets in cloud and network systems
-
Continuously validate your security controls for effective remediation
Why CTEM is Important?
Keeping pace with the rapidly changing threat landscape is tough - there are always new threats to respond to and vulnerabilities to patch.
By validating the effectiveness of your controls and process with attack simulation, Picus helps you understand which threats pose the greatest risk and take action to mitigate any exposures they are likely to exploit.
.png?width=950&height=540&name=Turn%20Threats%20Into%20Exposures%20(1).png)
Evolving Threat Landscape
Cyber-attacks are no longer isolated or simplistic—they are complex, coordinated, and continuously evolving. Sophisticated threat actors now leverage advanced techniques like living-off-the-land attacks and supply chain compromises, making detection and prevention harder than ever.
Limitations of Traditional Security
Static defenses and periodic assessments fail to keep up with the pace of modern threats. Traditional security methods often miss real-world attack paths and provide limited visibility into whether existing controls can stop today’s adversaries.
Adaptive Cybersecurity Posture
To stay resilient, organizations must continuously adapt to new vulnerabilities and attack techniques. CTEM supports this shift by validating exposures in real time and enabling rapid response across cloud, network, and hybrid environments.
Benefits of Proactive Cybersecurity
By focusing on validation and exploitability, CTEM empowers security teams to address critical risks before they’re exploited. This proactive approach improves threat readiness, reduces response time, and strengthens your overall security posture.
Benefits of a Continuous Threat Exposure Management Program
down silos.
security improvements.
66% Fewer Breaches with CTEM
Organizations prioritizing their security investments based on a continuous threat exposure management program will realize a two-third reduction in breaches.
Five Stages of a CTEM Program
Build a continuous, structured approach to managing exposures across your enterprise.
Picus supports every stage of the CTEM cycle, from scoping to validation, helping you turn visibility into action.
Scoping
Identify and define the critical assets, environments, and business functions to be evaluated. This sets the foundation for exposure management.
Discovery
Map the assets, vulnerabilities, misconfigurations, and potential attack paths across your enterprise, cloud, and hybrid environments.
Prioritization
Focus on exposures that are most likely to be exploited. Use threat intelligence, asset criticality, and exploitability to rank risks.
Validation
Simulate real-world attacks to confirm which exposures are truly exploitable in your environment. This step turns assumptions into evidence.
Mobilization
Take action to remediate validated exposures and improve defenses. Mobilization also includes ongoing communication between security and IT teams.
Why Choose Picus for CTEM?
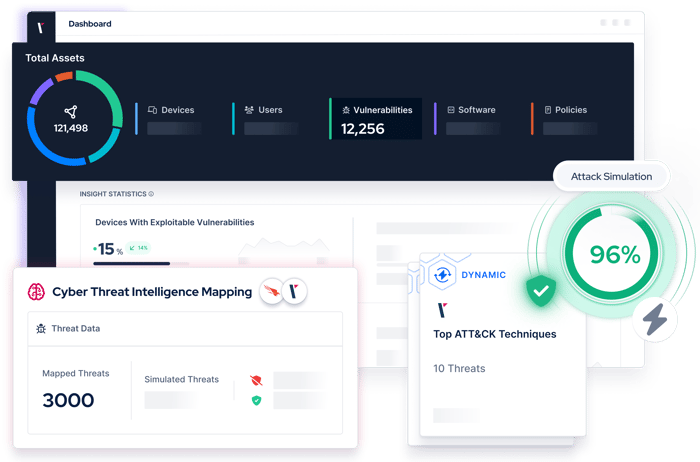
Picus helps security teams operationalize the CTEM lifecycle with adversarial exposure validation at its core. From identifying exposures to confirming exploitability and driving response, Picus enables teams to focus on validated risks and act with confidence.
Scoping:
Picus enables flexible and comprehensive CTEM scoping by validating exposures across on-premises, cloud, and hybrid environments. With its broad coverage, Picus ensures nothing is out-of-scope. From targeted assessments to organization-wide validation, security teams can implement their CTEM program wherever it matters most.
Discovery
Picus uncovers organizations’ attack surface by discovering both known and unknown assets within their CTEM scope. By integrating with vulnerability assessment and attack surface management technologies, Picus expands visibility beyond CVEs, identifying misconfigurations, insecure services, and other vulnerabilities that traditional tools often miss. The platform maps potential attack paths to highlight exposures that could lead to the compromise of critical assets.
Prioritization
Picus helps security teams prioritize exposures based on the potential impact on their environment. The platform dynamically adjusts risk levels, taking into account critical factors such as exploitability, ease of attack, and the context of business-critical assets. This allows security teams to prioritize the highest-impact exposures, ensuring that resources are focused on mitigating the threats that pose the greatest risk to the organization.
Validation
Picus validates exposures with its leading Adversarial Exposure technologies, including Breach and Attack Simulation (BAS) and Automated Penetration Testing (APT). By simulating real-world attack scenarios, Picus not only confirms the exploitability of identified vulnerabilities but also tests the effectiveness of existing security controls. The platform ensures that security teams focus on the most critical and validated exposures, avoiding wasted efforts on futile pursuits.
Mobilization
Picus delivers detailed and actionable reports that provide clear insights into potential risks, empowering security teams to take targeted action with confidence. The platform offers comprehensive remediation guidance, including vendor-specific prevention signatures and detection rules tailored to the environment in the CTEM scope. By automating remediation workflows through seamless integrations with ticketing and issue-tracking tools, Picus streamlines the process of addressing exposures. After fixes are applied, Picus re-validates exposures to ensure that the mitigations are effective and risks are reduced. Through clear and consistent reporting, Picus ensures that mobilization efforts are not only tracked but also continuously refined, allowing security teams to measure progress and improve their security posture over time.
Prioritize the Exposures That Matter
Siloed approaches make it difficult to manage your threat exposure successfully.
In a single platform, Picus supplies the context you need to make better security decisions across all areas of your security program.
Security validation insights, combined with data from the threat landscape and your attack surface, enable you to focus remediation and mitigation in the areas that matter.

Awarded by the Industry
Customer's Choice
2025 Gartner Peer Insights Voice of the Customer for Adversarial Exposure Validation
What Our Customers Say
Picus is very good attack simulation tool in overall. It shows all security vulnerabilities and guides..
Sr. Information Security & Risk Officer
The implementation was very fast, the platform is easy to integrate and results quite intuitive to be analyzed.
CIO
A very successful platform where we can test the accuracy of our security investments and see their scores.
Manager, IT Security and Risk Management
Picus is one of the best BAS solution on the market today. The threat database it is constantly updated..
ICT Security Engineer
There is a very nice team from which I can get quick support. The application provides us with great convenience and confidence in our work.
Information Security Specialist
With the help of this product we can perform continuosly endpoint attack via latest tactics and techniques which are used by threat actors..
Manager, IT Security and Risk Management
.. It is possible to customise the campaign or schedule the assessment periodically, to test protection measure implemented on network, endpoint and email.
ICT Security Engineer
Picus is such a great product for organizations that are looking to have constant checks and validation on their security posture in the organization.
Cybersecuirty Pre-sales Engineer
Picus is a real safety measurement tool. Ever since we took Picus into our inventory, Security has helped significantly to increase our maturity level.
Cyber Defense Senior Specialist
It strengthened our security perspective and allowed us to follow trend attacks. We can test zeroday malicious threats very early because Picus could add them their attack database quickly.
Security Specialist
Simulate Attacks to Reduce Your Threat Exposure
Use Cases
Enhance effectiveness across your security operations.
Improve decision making with a holistic view of your security posture.
Attack
Simulation
Simulate attacks to measure and optimize security controls.
Testing
Automation
Stay on top of exposures while alleviating manual testing requirements.
Resources
Latest CTEM News and Content
.png?width=353&height=200&name=Picus-gartner-reprint-march10-1%20(1).png)


.png?width=353&height=200&name=vulnerability-vs-exposure-blog-preview%20(1).png)




.png?width=3200&height=323&name=Pattern(1).png)
See the
Picus Security Validation Platform
Request a Demo
Submit a request and we'll share answers to your top security validation and exposure management questions.
Get Threat-ready
Simulate real-world cyber threats in minutes and see a holistic view of your security effectiveness.
Frequently Asked Questions
Continuous Threat Exposure Management (CTEM) is an approach to cyber security designed to help organizations obtain the context they need to prioritize exposures and manage risks more effectively.
Practically every security and IT team needs help to keep up with essential tasks such as vulnerability management. By combining data from the threat landscape and attack surface with vulnerability and security validation insights, CTEM helps organizations determine which exposures pose the greatest risk.
Garner’s CTEM definition comprises five cycle steps: scoping, discovery, prioritization, validation, and mobilization.
A traditional approach to vulnerability management involves prioritizing common vulnerabilities and exposures (CVEs) according to their CVSS score. A limitation of this approach, however, is that a severity score is not a rating that applies across all organizations - it can also be influenced by factors such as the number of assets affected, security controls coverage, and attack paths.
Continuous Threat Exposure Management helps overcome the limitations of traditional approaches to vulnerability management by facilitating a more holistic view and providing additional context to help security teams determine which exposures to prioritize.
Adopting a Continuous Threat Exposure management approach can require significant time and effort. To ease the process, it’s sensible to break the process into manageable steps.
Picus recommends a four-stage process: Discover, Validate, Prioritize, Optimize. By enriching security validation insights with threat intelligence, asset data, and vulnerability insights, our platform aggregates the information required to obtain a more holistic view and helps mitigate high-risk exposures swiftly and effectively.
Security validation is a core component of Continuous Threat Exposure Management because it enables security teams to quantify the effectiveness of security controls and processes.
For instance, by understanding if security controls are successfully configured to protect assets by blocking the exploitation of CVEs, security teams can obtain the additional insights they need to manage risks and prioritize the remediation of vulnerabilities.
The time it takes to adopt a Continuous Threat Management approach varies between organizations and can depend upon factors such as an organization’s existing maturity, controls, and resources.
Adopting CTEM by integrating multiple tools, such as Threat Intelligence, Attack Surface Management, Vulnerability Scanning and Breach and Attack Simulation solutions can create additional complexity and extend the adoption period by months.
For organizations that want to speed up the adoption of CTEM, unified platforms that offer broad functionality and integrate with a wide range of controls can speed up the process significantly.
.png?width=161&height=136&name=gartner-logo-2025%201%20(1).png)
