Validate Your Security Controls.
Prove Your Compliance
Centralized Validation for HIPAA, DORA, NIST, SOX, PCI DSS & CCoP 2.0 requirements.

Compliance Isn’t Documentation. It’s Control Effectiveness.
Many organizations treat audits as a paperwork exercise, relying on policies and screenshots to demonstrate compliance. But regulators increasingly expect evidence that controls work under real attack conditions. Validation bridges the gap between written compliance and operational resilience.
Stay Secure and Compliant at All Times
Learn how organizations continuously validate security posture and maintain compliance with provable results at all times.
Audit-Ready Evidence
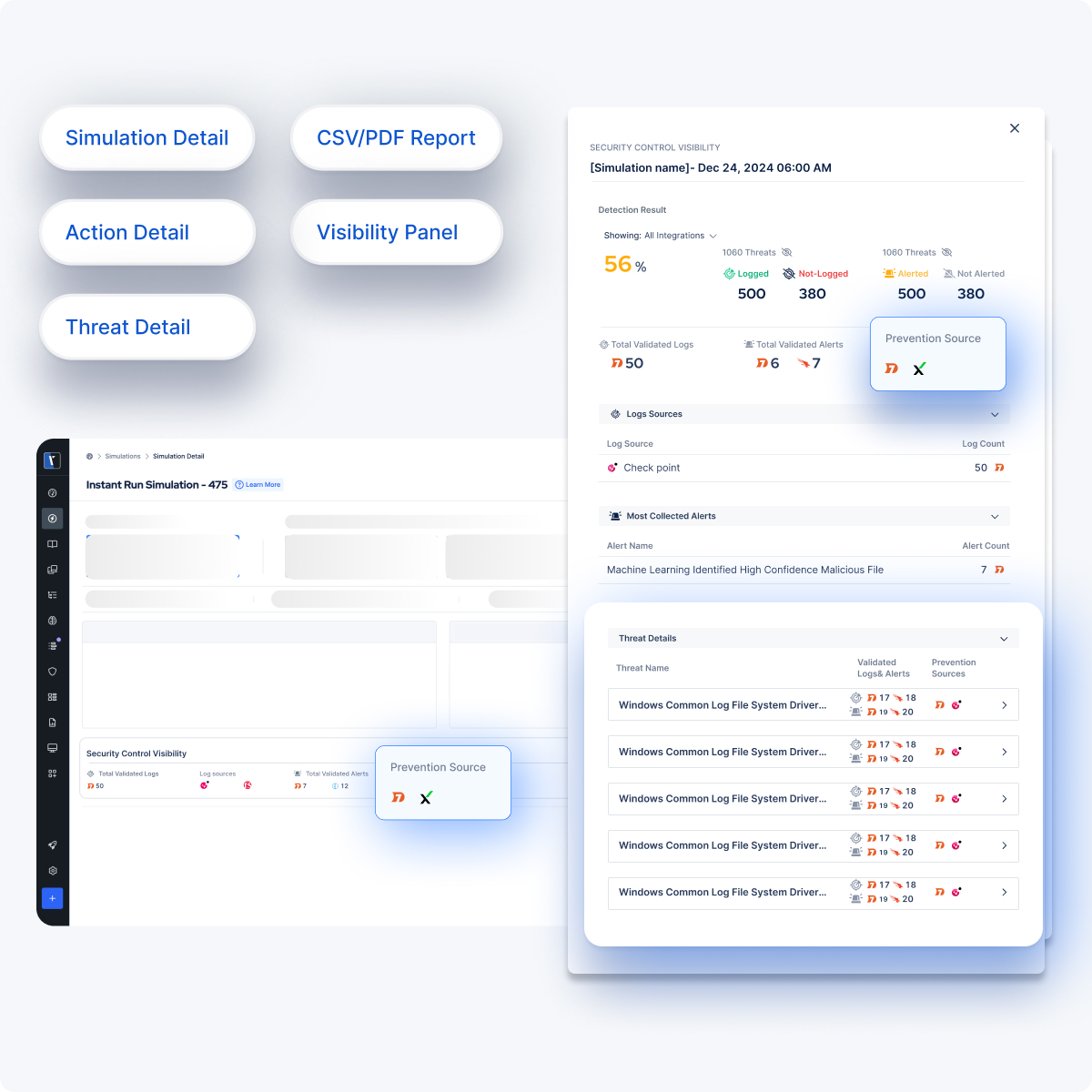
Turn Validation Results into Compliance Proof
Move beyond screenshots and static documentation. Generate structured, regulator-aligned reports that demonstrate control effectiveness under real-world attack conditions.
Explore Compliance Frameworks
Validate your security controls against real-world attack techniques and align results directly with regulatory requirements. From resilience testing to data protection and risk governance, demonstrate measurable compliance across on-premise, cloud, and hybrid networks.
RESOURCES
Compliance Insights




.png?width=3200&height=323&name=Pattern(1).png)
See the
Picus Security Validation Platform
Request a Demo
Submit a request and we'll share answers to your top security validation and exposure management questions.
Get Threat-ready
Simulate real-world cyber threats in minutes and see a holistic view of your security effectiveness.