How to Build a Red Teaming Attack Scenario | Part 1 - Bypass Security Controls
LAST UPDATED ON MAY 08, 2025
An attack scenario is a logical sequence of the Techniques, Tactics, and Procedures (TTPs) used by adversaries to launch cyberattacks and achieve their goals. At Picus Labs, we create attack scenarios in a structured format and run these scenarios to test security controls’ effectiveness against these attacks. This practice is very similar to adversary emulation, a type of red team engagement that mimics a known threat.
Red teams build scenarios to test certain aspects of an adversary’s TTPs for adversary emulation. So, developing attack scenarios is an essential part of a Red Team operation. Depending on the engagement’s complexity, Red Teams may spend weeks deciding which TTPs they will use to develop scenarios. This blog post aims to provide insight into the design and development phase of an attack scenario.
We chose a sample cyberattack to show how we construct an attack scenario. In this scenario, the attack bypasses security controls and opens a reverse shell. The execution flow of this attack scenario briefly includes the following actions:
- Initial access: The victim downloads a (malicious) fake installer of legitimate software.
- The victim executes the downloaded fake installer.
- The fake installer extracts malicious BAT and DLL files, then triggers the execution of these files.
- The extracted DLL is executed.
- The Common Language Runtime Hooking technique is used to bypass security controls and execute the malicious DLL file.
- Executed DLL downloads and runs a meterpreter payload
- The Process Hollowing sub-technique of the Process Injection technique is used to run the meterpreter reverse shell.
- The DLL file creates a werfault.exe process under the spoolsv.exe process.
- The DLL file utilizes the Blockdll technique to prevent the analysis of security controls.
- The malicious DLL file downloads the meterpreter shellcode from the C2 server.
- The DLL file injects and executes the downloaded meterpreter payload into werfault.exe.
Start your 14-day Free Trial: Simulate MITRE ATT&CK Techniques in minutes
We will explain how to identify and use these actions in the following sections.
1. Initial Access and Execution of the First Stage Payload
In this step, the victim user downloads a fake installer of legitimate software, then executes it. This fake installer masquerades itself as known legitimate software, such as anti-malware [1], Zoom [2], Adobe Flash Player [3], VPN [4], or online game installer [5].
Drive-by Compromise [6], Phishing [7], and Supply Chain Compromise [8] techniques are suitable for Initial Access for this scenario. We didn’t define a specific initial access technique for this scenario as any of them can be used.
The victim user executes the downloaded file, which extracts a malicious BAT and DLL file to the current directory and triggers the execution of these files.
MITRE ATT&CK Framework Techniques and Tactics:
|
MITRE ATT&CK Technique |
MITRE ATT&CK Tactic(s) |
|
T1189 Drive-by Compromise |
Initial Access |
|
T1566.001 Phishing: Spearphishing Attachment |
Initial Access |
|
T1566.002 Phishing: Spearphishing Link |
Initial Access |
|
T1195.002 Supply Chain Compromise: Compromise Software Supply Chain |
Initial Access |
2. Defense Evasion via DLL Side-Loading
Running a malicious and unsigned executable can be easily detected and blocked by security products. So, we try to avoid running an unsigned .exe file after the first execution of the fake installer to create an execution flow that can emulate a malicious installer’s behavior.
We chose DLL Side-Loading for Defense Evasion. It is a sub-technique of MITRE ATT&CK T1574 Hijack Execution Flow technique that enables attackers to run code on the target machine without spawning new suspicious processes. We can run our malicious codes, which are compiled as DLLs, inside a legitimate Windows process by using the DLL Side-Loading sub-technique.
Common Language Runtime (CLR) Hooking via stordiag.exe
There are different methods to employ DLL Side-Loading. For example, the security researcher Casey Smith presented a DLL Side-Loading method that can hijack the execution flow of .NET programs during the startup process. This method is called Common Language Runtime Hooking and makes it possible to use any .NET executable for execution without depending on heavily monitored Lolbas binaries [9]. In this attack scenario, we chose the CLR Hooking method.
Common Language Runtime (CLR) is a run-time environment of the .NET Framework that runs the code [10]. Services and configuration options provided by CLR make the development process easier. However, these services and configurations are also used by adversaries. For example, the CLR Hooking method uses the Application Domain Manager configuration.
When a .NET program is started, CLR is going to search for the DLL containing the Application Domain Manager (ADM), which is defined by the attacker with environmental variables. A custom ADM can be configured to be used by CLR by setting specific environment variables: APPDOMAIN_MANAGER_ASM and APPDOMAIN_MANAGER_TYPE [11]. An adversary may use these variables to redirect execution to a malicious code provided by her/him before the execution of the actual program starts.
Utilizing the CLR Hooking method, attackers can use any .NET binary to load a malicious DLL while avoiding direct execution of an EXE file. In our scenario, we will use stordiag.exe binary to load our malicious DLL.
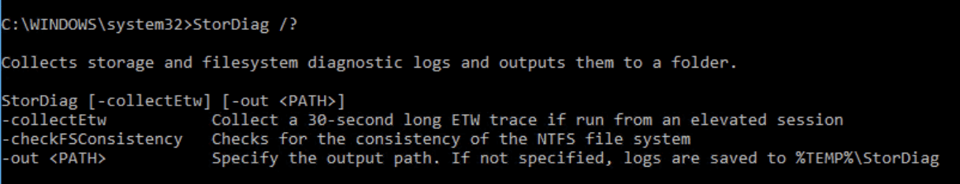
Stordiag.exe is a command-line utility that analyzes storage on devices running Windows 10. We used the below commands in the attack scenario to test CLR Hooking step separately. For a more detailed explanation, see this blog [12].
|
copy %TMP%\DomainManager.dll \Windows\System32 |
|
set APPDOMAIN_MANAGER_ASM=DomainManager, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null |
|
set APPDOMAIN_MANAGER_TYPE=DomainManager.InjectedDomainManager Stordiag.exe |
MITRE ATT&CK Techniques and Tactics:
|
MITRE ATT&CK Technique |
MITRE ATT&CK Tactic(s) |
|
T1574.002 Hijack Execution Flow: DLL Side-Loading |
Defense Evasion, Privilege Escalation |
3. Defense Evasion via Process Injection
We invoked our second-stage payload, DomainManager.dll, with CLR hooking in the previous step. In this step, we need to create an execution flow to download and execute our actual payload, which is a meterpreter shellcode. You can use another payload for execution.
Separating a malicious code into different stages is useful to avoid detection by security controls, especially ones that use static rules. Therefore, we chose to execute our actual payload as the third stage from memory without writing it on the filesystem.
A host process is required to execute the shellcode from memory and run the shellcode under one of its threads. We are going to inject our shellcode into this host process by using the second stage DLL, DomainManager.dll. So, we will use the Process Injection technique for defense evasion in this step. See our blog post about Process Injection methods, use cases, red and blue team exercises, Sigma rules, and IBM Qradar and Splunk SPL queries for the Process Injection technique [13].
From the offensive security perspective, attackers can try to blend in with the target environment to decrease the chances of detection. Choosing execution paths that resemble the standard user/machine behavior is important to design more evasive scenarios.
Start your 14-day Free Trial: Simulate MITRE ATT&CK Techniques in minutes
Werfault.exe Injection
We chose Werfault.exe to build a more evasive scenario. Werfault.exe is the Windows Error Reporting binary used by many different programs to report errors [14]. If something on a Windows system crashes, Werfault.exe allows the crash report to be forwarded to Microsoft.
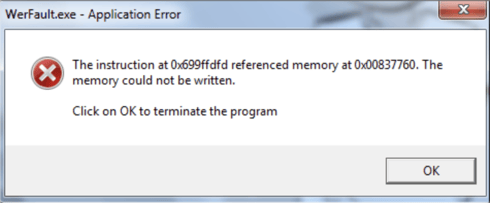
Werfault.exe process occasionally spawns when an application crashes. Due to this behavior, the parent process of Werfault.exe can be arbitrary, which makes it harder to detect malicious behavior with respect to parent-child process relations. For that reason, malware families like Netwire RAT, Cerber ransomware, Kraken loader, Azorult info-stealer, and Lokibot are observed to be using Werfault.exe as the target of injection [15].
Parent PID Spoofing
We can bypass the security controls that monitor suspicious parent/child process relations by mimicking a standard system behavior with Werfault.exe as the target process of injection. Parent/child relations can also be modified using the Parent PID Spoofing sub-technique of the MITRE ATT&CK T1134 Access Token Manipulation technique, which enables us to control the Parent PID of our target process. By spoofing Parent PID of Werfault.exe, we create a parent/child relationship as if a standard Windows process spawns the Werfault.exe.
Blockdlls Method
When deploying malicious code on a target system, attackers need to defend their code against the security products. An interesting method is blockdlls, which is explained in a research article by Adam Chester [16]. The article explains the blockdlls method and gives detailed information about how a process can be protected from endpoint security products loading their user-mode code via a DLL. We will utilize this method to prevent security controls from loading DLLs into Werfault.exe for analysis [17]. See our Impair Defenses blog post about how attackers disables, modifies, and blocks defensive security controls.
Process Hollowing
We use a gist for the Werfault.exe injection with Parent PID Spoofing and blockdlls [17]. We also use Process Hollowing for injection, which is a sub-technique of MITRE ATT&CK T1055 Process Injection technique. It is suitable for use in our attack scenario since it creates a new process in a suspended state for modifying its memory.
|
Win32.CreateProcess( |
UpdateProcThreadAttribute API call is used for changing the Parent PID of the new process and implementing the blockdlls method.
|
Marshal.WriteIntPtr(lpValue, new IntPtr((long)Win32.BinarySignaturePolicy.BLOCK_NON_MICROSOFT_BINARIES_ALLOW_STORE)); |
|
Win32.UpdateProcThreadAttribute( |
The original code uses a hard-coded Command and Control (C2) address for downloading the shellcode into the memory. We can change it to an arbitrary environment variable since we already need to change some environment variables for the CLR Hooking. To combine CLR Hooking and Process Hollowing methods, we can use the injection code in a custom Application Domain Manager DLL to create a remote shellcode loader starting with CLR Hooking. You can download the source code of Custom Domain Manager DLL, including injection code from our Github repository [18].
MITRE ATT&CK Framework Techniques and Tactics:
|
MITRE ATT&CK Technique |
MITRE ATT&CK Tactic(s) |
|
1055.012 Process Injection: Process Hollowing |
Defense Evasion, Privilege Escalation |
|
T1562.001 Impair Defenses: Disable or Modify Tools |
Defense Evasion |
|
T1134.004 Access Token Manipulation: Parent PID Spoofing |
Defense Evasion, Privilege Escalation |
We described initial access, execution of the first stage payload, and defense evasion (process injection, blockdlls method, parent PID spoofing) stages of our attack scenario in this first part of this blog series. In the second part, we explained weaponization, shell code download, clearing tracks, and connecting parts to create the attack scenario.
References
|
[1] “Beware! Fake antivirus installer caught distributing cryptocurrency malware,” 25-Aug-2020. [Online]. Available: https://news.thewindowsclub.com/beware-fake-malwarebytes-antivirus-installer-caught-distributing-cryptocurrency-malware-102523/. [Accessed: 13-Oct-2020] [2] L. Abrams, “PSA: Fake Zoom installers being used to distribute malware,” BleepingComputer, 06-Apr-2020. [Online]. Available: https://www.bleepingcomputer.com/news/security/psa-fake-zoom-installers-being-used-to-distribute-malware/. [Accessed: 13-Oct-2020] [3] J. Long, “Adobe Flash Player is dead, yet 10% of Macs are infected with fake Flash malware,” 31-Jan-2020. [Online]. Available: https://www.intego.com/mac-security-blog/adobe-flash-player-is-dead-yet-10-of-macs-infected-with-fake-flash-malware/. [Accessed: 13-Oct-2020] [4] D. Bisson, “AZORult Trojan Disguised Itself as Fake ProtonVPN Installer,” 18-Feb-2020. [Online]. Available: https://www.tripwire.com/state-of-security/featured/azorult-trojan-disguised-itself-as-fake-protonvpn-installer/. [Accessed: 13-Oct-2020] [5] D. Olenick, “Lokibot now using fake Epic Games installer to fool victims,” 18-Feb-2020. [Online]. Available: https://www.scmagazine.com/home/security-news/malware/lokibot-now-using-fake-epic-games-installer-to-fool-victims/. [Accessed: 13-Oct-2020] [6] “Drive-by Compromise.” [Online]. Available: https://attack.mitre.org/techniques/T1189/. [Accessed: 13-Oct-2020] [7] “Phishing.” [Online]. Available: https://attack.mitre.org/techniques/T1566/. [Accessed: 13-Oct-2020] [8] “Supply Chain Compromise.” [Online]. Available: https://attack.mitre.org/techniques/T1195/. [Accessed: 13-Oct-2020] [9] “Common Language Runtime Hook for Persistence.” [Online]. Available: https://www.contextis.com/en/blog/common-language-runtime-hook-for-persistence. [Accessed: 14-Oct-2020] [10] gewarren, “Common Language Runtime (CLR) overview.” [Online]. Available: https://docs.microsoft.com/en-us/dotnet/standard/clr. [Accessed: 14-Oct-2020] |
[11] dotnet-bot, “AppDomainManager Class.” [Online]. Available: https://docs.microsoft.com/en-us/dotnet/api/system.appdomainmanager. [Accessed: 14-Oct-2020] [12] 3gstudent, “Use AppDomainManager to maintain persistence.” [Online]. Available: https://3gstudent.github.io/Use-AppDomainManager-to-maintain-persistence/. [Accessed: 14-Oct-2020] [13] S. Özarslan, “MITRE ATT&CK T1055 Process Injection.” [Online]. Available: https://www.picussecurity.com/blog/picus-10-critical-mitre-attck-techniques-t1055-process-injection. [Accessed: 14-Oct-2020] [14] A. B. Santos, “The werfault.exe enables Microsoft to track and handle errors relating to the OS and Windows features. Here’s how to fix the Werfault.exe Application Error.” [Online]. Available: https://softwarekeep.com/help-center/what-is-werfaultexe-and-how-to-fix-it-on-windows-10. [Accessed: 14-Oct-2020] [15] Threat Intelligence Team, “Release the Kraken: Fileless injection into Windows Error Reporting service,” 06-Oct-2020. [Online]. Available: https://blog.malwarebytes.com/malwarebytes-news/2020/10/kraken-attack-abuses-wer-service/. [Accessed: 14-Oct-2020] [16] A. Chester, “Protecting Your Malware with blockdlls and ACG.” [Online]. Available: https://blog.xpnsec.com/protecting-your-malware/. [Accessed: 14-Oct-2020] [17] 2625, “blockdlls_gadget2jscript.cs.” [Online]. Available: https://gist.github.com/rvrsh3ll/1e66f0f2c7103ff8709e5fd63ca346ac. [Accessed: 14-Oct-2020] [18] picussecurity, “picussecurity/picuslabs.” [Online]. Available: https://github.com/picussecurity/picuslabs. [Accessed: 14-Oct-2020] |


.png?width=353&height=200&name=Ni8mare-ET-preview-oct25%20(1).png)






