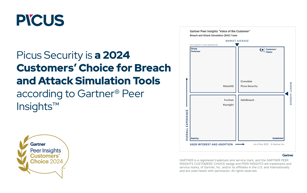
Picus Security recognized as a Customers’ Choice in the 2025 Gartner® Peer Insights™
Picus Security named #1 Breach and Attack Simulation (BAS) Solution by G2
The Report by Mastercard and Picus: Proving Cyber Resilience with Security Validation
Platform
I want to
Use Cases
Frameworks
Industry
RESEARCH
COMPANY