What Is the Cyber Kill Chain?
The Cyber Kill Chain is a cybersecurity framework that describes the stages a threat actor moves through when executing an attack. The model treats an attack as a linear sequence of steps.
The framework covers the full attack lifecycle. It starts before an attacker ever touches your systems, during the reconnaissance phase, and ends when they achieve their final objective, whether that is stealing data, deploying ransomware, or disrupting operations.

Figure 1. 7 Steps of Cyber Kill Chain
The core idea is that attackers need to complete all seven steps to succeed. Defenders only need to stop them once.
The Origins: Lockheed Martin's Cyber Kill Chain
The original "kill chain" concept comes from the U.S. military, where it described the process of identifying a target, making a decision to engage, and executing the strike.
In 2011, computer scientists at Lockheed Martin took an old idea and gave it new life in online security.
Today, the Cyber Kill Chain is a registered methodology of Lockheed Martin and remains a foundational tool for threat analysts and security architects worldwide.
The 7 Steps of the Cyber Kill Chain
A breach unfolds over time, never just one sudden event. Step by step, intruders advance, yet every stage opens a window for detection. Each move they make reveals something useful. Here are the 7 steps of the Cyber Kill Chain:
1. Reconnaissance
Reconnaissance refers to the first stage, where attackers gather information about your company before taking any visible action. They focus on three areas:
- Your people: LinkedIn profiles expose names, roles, and org structure.
- Your technology: Job postings reveal your tech stack. SSL certificates expose subdomains. HTTP response headers identify frameworks and servers.
- Your exposure: Port scans show what services you have open to the Internet.
2. Weaponization
Weaponization refers to the stage where attackers build or acquire a weapon tailored to what they found. This means pairing a malicious payload, such as a remote access trojan or ransomware, with a delivery mechanism like a malicious Office macro or a phishing link.
The attacker tailors the weapon to the specific vulnerabilities they discovered during reconnaissance.
3. Delivery
Delivery describes the point when the attacker gets their tool into your system.
Most often, that happens through phishing emails. Sometimes it arrives on a physical device like a USB stick left where someone might plug it in. Web apps exposed online also serve as entry points if flaws go unpatched.
4. Exploitation
Exploitation occurs when the delivered payload executes and takes advantage of a vulnerability.
This might be a software vulnerability in an unpatched application, a misconfiguration in your environment, or a user who clicks a link and allows code to run.
5. Installation
Installation marks the stage where the attacker places a persistent mechanism on the compromised system. This is typically a backdoor, a remote access tool, or a web shell.
The goal is to maintain access even if the initial entry point is closed.
6. Command and Control (C2)
Command and Control refers to the stage where the attacker sets up a remote communication channel with the compromised system. This allows them to issue commands, and exfiltrate data.
C2 traffic is often disguised as normal web traffic using HTTP, HTTPS, or DNS to avoid detection.
7. Actions on Objectives
Actions on Objectives is the final stage, where the attacker executes their goal.
Depending on their motivation, this could mean exfiltrating sensitive data, encrypting files for ransom, destroying systems, or establishing a persistent presence for future operations.
What Are the Benefits of the Cyber Kill Chain?
Here are the three key benefits of the Cyber Kill Chain:
- One language, no confusion: The Cyber Kill Chain gives your security team a shared language for describing attacks. When an analyst says "the attacker is in the C2 phase," everyone understands the severity and what to do next.
- Satisfies regulators: Under frameworks like GDPR and NIS2, the kill chain shows auditors you understand the attack lifecycle and have controls mapped to each stage.
- Pinpoints breach impact fast: When a breach occurs, analysts work backwards through the kill chain to determine how far the attacker progressed and what was affected.
Cyber Kill Chain vs. MITRE ATT&CK
The Cyber Kill Chain and the MITRE ATT&CK framework are both widely used to understand and defend against cyber threats, but they serve different purposes and operate at different levels of detail.
The table below breaks down the key differences:
Cyber Kill Chain | MITRE ATT&CK | |
Created by | Lockheed Martin (2011) | MITRE Corporation (2013) |
Structure | 7 linear phases | 14 tactic categories with hundreds of techniques |
Attack flow | Sequential, step-by-step | Non-linear, flexible |
Level of detail | High-level overview | Granular TTPs (Tactics, Techniques, Procedures) |
Update frequency | Static since 2011 | Continuously updated with real-world attack data |
Best used for | Strategic defense planning | Threat detection and hunting |
Three Cyber Kill Chain Challenges
The Cyber Kill Chain was designed in 2011. The threat environment has changed. You need to know its limits before you build your security strategy around it.
Here are three limitations of Cyber Kill Chain:
- Linear attack assumption: Sophisticated attackers, especially APT groups, do not follow a strict sequence. They loop back, skip phases, or run multiple kill chains simultaneously across your infrastructure.
- Malware and perimeter focus: The framework does not address insider threats. A malicious employee already has authorized access and skips the early phases entirely.
- Over-investment in prevention: Focusing on stopping initial access leads organizations to under-invest in detection and response. When an attacker gets past your perimeter, you need controls to catch them quickly.
Treat the Kill Chain as a starting point. Supplement it with MITRE ATT&CK and controls that cover insider threats and credential-based attacks.
How to Validate Your Security Stack Against the Full Adversarial Kill Chain
Understanding the Cyber Kill Chain is one thing, but understanding whether your security controls would actually stop the attacker moving along the chain is another.
Most organizations believe their security controls are working as intended, but Picus tests whether this is true.
How Does Picus Platform Run Attack Simulations Across Full Adversarial Kill Chain?
Picus Security Control Validation, powered by Breach and Attack Simulation (BAS), runs continuous and automated attack simulations to test your defenses against real-world attacker techniques.
At the core of the platform is the Picus Threat Library, maintained by Picus Labs and continuously updated with threat actor campaigns, malware behaviors, and newly disclosed CVE exploits.
All simulations are mapped to MITRE ATT&CK, the industry standard for understanding attacker behavior. While the Cyber Kill Chain shows seven high-level stages, MITRE ATT&CK provides detailed tactics and techniques that reveal exactly how attacks occur and how security controls respond.
For teams that prefer a kill-chain perspective, Picus also supports filtering by the Unified Cyber Kill Chain.
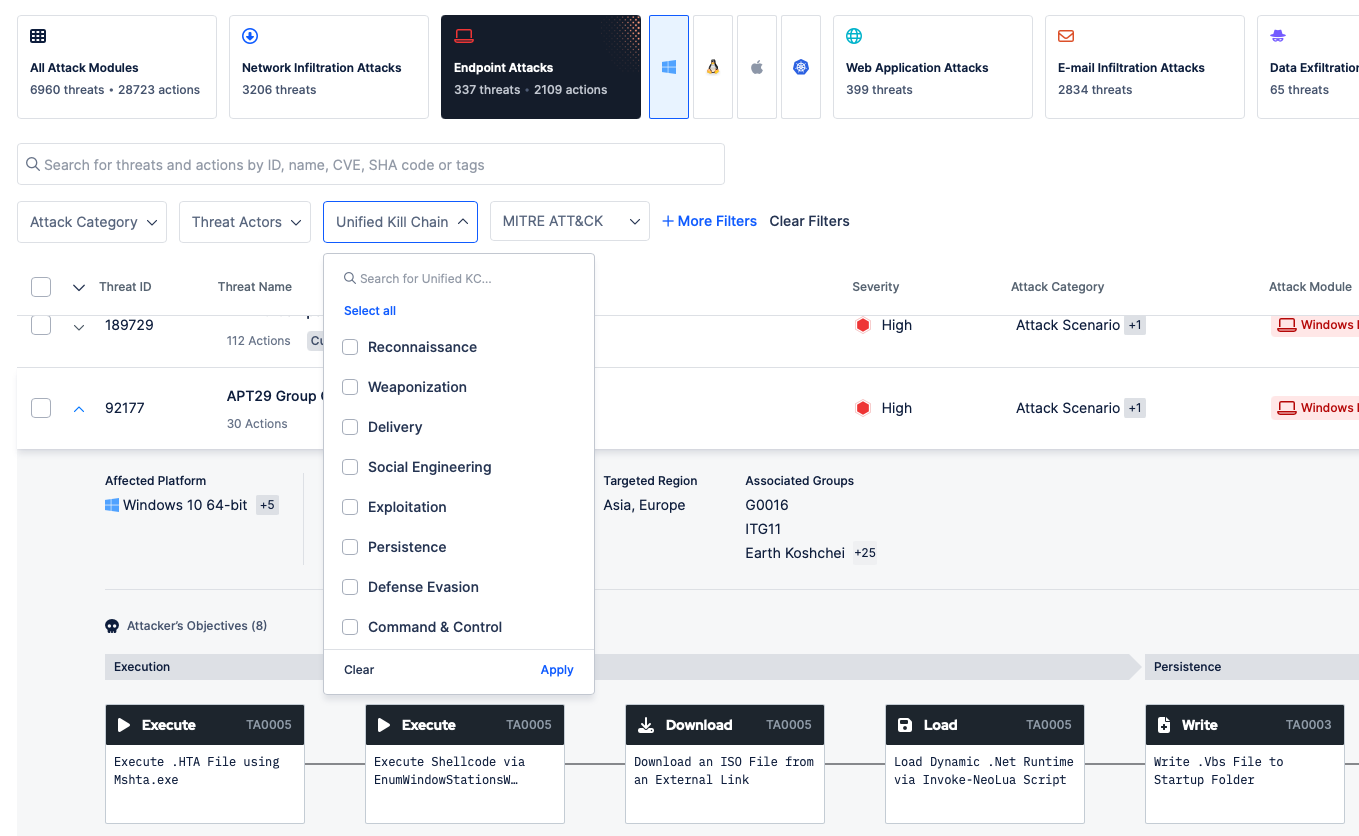
Figure 2. Simulations mapped to MITRE ATT&CK
The result is precise visibility into which techniques are:
- Prevented by security controls
- Detected by monitoring systems
- Completely missed by the security stack
This approach mirrors the way modern exposure validation platforms prove how attacks could realistically exploit security gaps.
However, identifying a security gap is only the first step. What matters most is how quickly it can be fixed. After each simulation run, the Picus Mitigation Library provides ready-to-use remediation guidance tailored to your security stack.
This includes:
- Vendor-specific prevention signatures for technologies such as firewalls, IPS, and WAF
- Detection rules for SIEM, EDR, and XDR platforms
- Standardized rule formats such as SIGMA for cross-platform compatibility
Instead of leaving teams with a long list of findings, Picus delivers clear, actionable fixes that can often be deployed with a single click.
Get your free demo now, fix the gaps in your security investments!
Key Takeaways
- The Cyber Kill Chain breaks every attack into 7 sequential phases: Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control (C2), and Actions on Objectives. Attackers must complete all seven steps to succeed. Defenders only need to stop them once.
- Lockheed Martin introduced the Cyber Kill Chain in 2011, adapting the U.S. military's target-engage-strike concept to cybersecurity. It is a registered methodology of Lockheed Martin and a foundational tool for threat analysts worldwide.
- The framework has real limits. It assumes a linear attack path, which sophisticated threat actors do not always follow. It also does not adequately address insider threats, since a malicious insider already has authorized access and bypasses the early phases entirely.
- The Cyber Kill Chain gives security teams a shared language for analyzing and communicating about attacks. It also supports compliance with frameworks like GDPR and NIS2 by showing regulators that your organization has controls mapped to each attack phase.
- The Cyber Kill Chain provides a high-level view. MITRE ATT&CK goes deeper, with 14 tactic categories and hundreds of specific techniques. For example, MITRE ATT&CK also covers Lateral Movement and Exfiltration as distinct phases, which the Cyber Kill Chain does not.
- Picus maps simulations to MITRE ATT&CK and Picus Security Validation Platform tests whether your controls would actually stop an attacker at each phase. The Picus Mitigation Library delivers ready-to-use fixes, including vendor-specific signatures and detection rules for firewalls, IPS, SIEM, and EDR platforms.
Frequently Asked Questions
Q: What is a cyber kill chain?
A: The Cyber Kill Chain is a cybersecurity framework describing the linear sequence of steps a threat actor moves through during an attack. It breaks an attack down into seven distinct phases. If a defender can interrupt any one of those steps, the entire attack fails.
Q: What are the 7 stages of the Cyber Kill Chain?
A: The seven stages are Reconnaissance, Weaponization, Delivery, Exploitation, Installation, Command and Control (C2), and Actions on Objectives. An attacker must complete all seven steps to succeed. Defenders only need to stop the attacker once.
Q: What happens at the beginning of a cyber kill chain?
A: The framework starts with the reconnaissance phase before an attacker touches your systems. Attackers collect details about your company by mapping out visible systems. This includes checking staff names online for email formats, scanning networks for open ports, and reading job ads for software clues.
Q: What is exploitation in a cyber kill chain?
A: Exploitation happens when a delivered payload executes and takes advantage of a vulnerability. This can be a software vulnerability in an unpatched application, an environment misconfiguration, or a user clicking a link that allows malicious code to run.
Q: Who created the cyber kill chain?
A: The original kill chain concept comes from the U.S. military. In 2011, computer scientists at Lockheed Martin applied this idea to online security. Today, the methodology remains a registered tool of Lockheed Martin.
Q: What is the purpose of the cyber kill chain model?
A: The model gives security teams a shared language for analyzing attacks. It also helps organizations demonstrate proactive security measures for compliance frameworks like GDPR, and improves incident response by helping analysts track attacker progression.


.png?width=353&height=200&name=Ni8mare-ET-preview-oct25%20(1).png)






