What Are Living Off the Land (LOTL) Attacks?
| March 25, 2026
Key Takeaways
- 84% of high-severity attacks use LOTL techniques. Malware-free attacks account for 79% of all detections, up from 40% in 2019.
- LOTL attacks use trusted, pre-installed tools: PowerShell, WMI, certutil, rundll32, and scheduled tasks. Traditional antivirus tools relying on file scanning won't stop them.
- PowerShell appears in 71% of documented LOTL cases. Attackers use it to download payloads, run code in memory, disable defenses, and move laterally.
- LOTL attackers stay hidden for a long time. Volt Typhoon maintained access in victim environments for at least five years before detection.
- Effective detection requires behavioral analytics, not signatures. Enable PowerShell logging, monitor unusual parent-child process relationships, and build detection rules for known LOLBin abuse using MITRE ATT&CK.
- Picus Security Control Validation runs real LOTL simulations against your production environment. The Picus Mitigation Library then gives you the exact signatures, detection rules, and configuration changes needed to close the gaps.
Most attackers don't break in. They blend in.
They use the same tools your IT team uses every day: PowerShell, Windows Management Instrumentation (WMI), scheduled tasks, and built-in command-line utilities. No custom malware. No obvious indicators of compromise. Just trusted system tools doing suspicious things.
Living-off-the-land (LOTL) attacks have become the dominant method for sophisticated threat actors. According to an analysis of 700,000 security incidents by Bitdefender, 84% of high-severity attacks involve LOTL techniques [1]. CrowdStrike's 2025 Global Threat Report puts the broader malware-free attack rate at 79% of all detections, up from 40% in 2019 [2].
If your defenses rely on spotting only malicious files, you're already behind.
What Is a Living-Off-the-Land (LOTL) Attack?
A living-off-the-land attack is a cyberattack technique where adversaries use legitimate, pre-installed system tools to carry out malicious activities, instead of deploying custom malware.
Rather than introducing foreign software, attackers "forage" in your environment. They pick up tools that are already trusted by your operating system and security stack. That trust is exactly what makes these attacks so effective. Security controls are built to flag unknown files. They're not built to question why your system administrator just ran PowerShell at 2 a.m.
The term has been around since roughly 2013, but the technique is far older. What's changed is scale: LOTL is now the default mode for ransomware groups, nation-state actors, and cybercriminals alike.
How LOTL Attacks Work
LOTL attacks work because they exploit trust at every layer, such as trust in system tools and signed files. Each technique below targets a different form of that trust, and attackers rarely use just one.
Leveraging Preexisting Vulnerabilities
LOTL attacks don't start in a vacuum. Attackers typically gain initial access by exploiting a known vulnerability in a public-facing application, VPN, or unpatched system. Once inside, they switch to LOTL techniques to avoid detection.
Vulnerability exploitation as an initial access method jumped 34% year-over-year, now accounting for 20% of all breaches [3], highlighting how initial access via unpatched systems feeds directly into LOTL campaigns.
Exploiting Trusted System Tools
Attackers don't need to bring weapons. Every Windows system ships with powerful administrative utilities: PowerShell, WMI, certutil, rundll32, mshta, and more.
The LOLBAS project documents over 200 Windows binaries that can be weaponized. Attackers run these tools with malicious intent, but to your security stack, the process looks legitimate.
Hiding Malicious Code Within Benign Files
Attackers embed malicious logic inside legitimate-looking files: Office macros, HTML applications (HTAs), and encoded PowerShell commands. The files pass initial inspection because they're structurally normal. The malicious payload only activates when a user opens the file or when a triggered script decodes and executes it in memory.
This technique makes static analysis and signature-based detection largely ineffective.
Types of LOTL Attacks
LOTL attacks aren't a single technique. They're a family of approaches that share one principle: use what's already there. The specific method depends on what the attacker wants to achieve, whether that's persistence, evasion, lateral movement, or all three.
Here are the most common types you'll encounter in the wild.
Binary Planting
Binary planting, also known as DLL hijacking, involves placing a malicious file where a trusted application will load it automatically. When the legitimate application runs, it unknowingly executes the attacker's code. The attack exploits how Windows searches for and loads libraries, making it difficult to spot without careful monitoring of file paths and load activity.
Registry Run Keys
Attackers use Windows Registry Run keys to establish persistence. By adding a malicious entry to a registry key that executes on user login or system startup, they ensure their code runs automatically, without leaving an obvious file on disk. This technique is a staple of fileless persistence and is used by groups ranging from commodity malware to advanced persistent threats (APTs).
Fileless Malware
Fileless malware operates entirely in memory. It never writes a payload to disk, which means traditional antivirus tools that scan files won't find it. The code typically loads via a legitimate interpreter like PowerShell or WMI, executes its payload in RAM, and disappears after a reboot, unless it has also planted a persistent trigger via a registry key or scheduled task.
WannaMine is a real-world example. This fileless cryptomining worm uses PowerShell and WMI subscriptions to run entirely in memory, hijacking CPU resources without ever touching disk.
PowerShell-based Attacks
PowerShell is the most abused LOTL tool in the world, appearing in approximately 71% of all documented LOTL cases [4]. It gives attackers deep access to Windows internals: they can download payloads, execute code in memory, disable security tools, inject processes, and move laterally; all with a signed, built-in binary that most environments can't afford to block entirely.
Notable Real-World LOTL Attack Examples
Real-world breaches make the threat concrete.
Volt Typhoon
Volt Typhoon, which is a Chinese state-sponsored group, targeted U.S. critical infrastructure across the energy, telecom, and transportation sectors.
They used PowerShell, WMIC, netsh, and ntdsutil to conduct reconnaissance, steal credentials, and move laterally. No custom malware. In some victim environments, they maintained access for at least five years before discovery [5].
WannaMine Malware
WannaMine used LOTL techniques for cryptojacking. It spread via EternalBlue and credential theft, maintained persistence through WMI event subscriptions, and ran Monero mining code entirely in memory.
OilRig (APT34)
OilRig, an Iranian state-sponsored group active since 2014, built much of its tradecraft around abusing tools that no security team would think to block.
Their campaigns used certutil, a native Windows certificate management utility, for file transfer and decoding Base64-encoded payloads and pulling them from attacker-controlled infrastructure, all without triggering standard controls [6].
LOLDrivers: Living Off-the-Land Drivers
LOLDrivers is a community-driven project that catalogs signed Windows drivers with known vulnerabilities that attackers can abuse.
Most LOTL discussions focus on user-space tools like PowerShell. LOLDrivers are different: they operate at the kernel level. By loading a vulnerable but legitimately signed driver, an attacker can bypass security controls, disable endpoint protection, and execute code with the highest privileges the operating system offers.
Modern Windows requires drivers to be digitally signed. That's exactly what makes LOLDrivers so dangerous: the signatures are real. The drivers are trusted by the OS. Attackers exploit that trust to gain kernel access without triggering standard controls.
Tools Used by Cybercriminals in LOTL Attacks
These are the most commonly abused tools in LOTL campaigns:
- PowerShell downloads payloads, executes code in memory, disables defenses, and enables lateral movement.
- WMI (Windows Management Instrumentation) enables remote execution and persistent code execution via event subscriptions. Attackers use it to store malicious modules and trigger execution on system events.
- certutil.exe is a certificate management tool that attackers abuse to download remote files and decode Base64-encoded payloads, bypassing standard controls.
- rundll32.exe loads and executes functions within DLL files, making it a common tool for proxy execution of malicious code.
- mshta.exe executes HTML Application (HTA) files and is frequently used to run malicious scripts under the guise of a legitimate Windows binary.
- PsExec is a legitimate remote execution tool that attackers use extensively for lateral movement across environments.
- Scheduled Tasks allow attackers to establish persistence by scheduling malicious scripts to run at login or on a timer, surviving reboots without writing suspicious executables.
How to Detect LOTL Attacks
Detection starts with visibility. You can't catch what you can't see.
The core challenge is that LOTL attacks look like normal administrative behavior. Behavioral analytics closes that gap by establishing baselines and flagging deviations. Instead of asking "Is this file malicious?", it asks "Is this behavior normal?" That shift in logic is what makes it effective against LOTL, where the tools are clean, but the actions aren't.
Key detection approaches include:
- Enable comprehensive logging: PowerShell Script Block Logging and Module Logging capture the actual commands being run, not just the fact that PowerShell launched. Enable Windows Event Log forwarding to your SIEM and retain logs long enough to support threat hunting.
- Monitor process behavior: Look for unusual parent-child process relationships. A Word document spawning PowerShell is suspicious. PowerShell calling certutil to download a remote file is a red flag.
- Hunt for LOLBin abuse: Tools like certutil, mshta, and rundll32 have legitimate uses, but rarely in the combinations attackers favor. Create detection rules for their known abuse patterns using frameworks like MITRE ATT&CK.
- Validate your detection rules continuously: Knowing you have logging enabled isn't the same as knowing your detection rules are working. Security control validation through breach and attack simulation lets you run real LOTL attack scenarios against your environment and confirm whether your SIEM, EDR, and other controls actually generate alerts. If they don't, you'll find out before an attacker does.
How Picus Helps You Defend Against LOTL Attacks
Most organizations don't know whether their defenses actually stop LOTL attacks. They assume they do. Picus removes the assumption.
The Picus Security Control Validation solution, powered by Breach and Attack Simulation, runs real LOTL attack scenarios directly against your production environment, safely and continuously. Not a lab. Not a quarterly penetration test snapshot. Your actual controls, tested against actual adversary behavior, every single day.
Picus Threat Library contains thousands of attack simulations mapped to MITRE ATT&CK, including the full spectrum of LOTL techniques: PowerShell-based fileless execution, WMI persistence, certutil payload staging, registry run key abuse, LOLDriver exploitation, and more. Every simulation reflects how real threat actors operate today. When a new LOTL campaign emerges in the wild, Picus adds it to the library so you can test against it before it reaches your network.
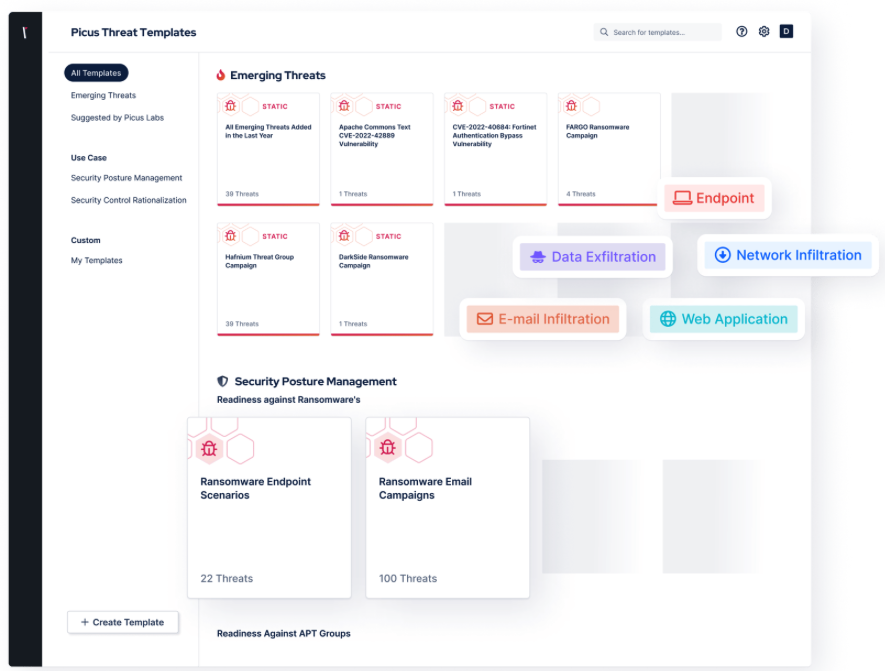
Figure 1. Picus Threat Library, Emerging Threats Templates
Picus Mitigation Library takes it a step further. When a simulation exposes a gap in your EDR, SIEM, or network controls, Picus doesn't just tell you something failed. It hands you the exact signatures, detection rules, and configuration changes needed to fix it, ready to deploy into your security stack.
The result is a continuous feedback loop: simulate → detect → fix → validate again. Your defenses get measurably stronger over time, and you always know exactly where you stand against LOTL threats. Not in theory. In practice.
Request a demo and see how Picus exposes the LOTL gaps your current stack is missing.
References
[1] “Living Off the Land: What We Learned from 700,000 Security Incidents,” The Hacker News. Accessed: Mar. 13, 2026. [Online]. Available: https://thehackernews.com/expert-insights/2025/05/living-off-land-what-we-learned-from.html
[2] “[No title].” Accessed: Mar. 13, 2026. [Online]. Available: https://go.crowdstrike.com/rs/281-OBQ-266/images/CrowdStrikeGlobalThreatReport2025.pdf?version=0
[3] K. Poireault, “Verizon’s DBIR Reveals 34% Jump in Vulnerability Exploitation,” Infosecurity Magazine. Accessed: Mar. 13, 2026. [Online]. Available: https://www.infosecurity-magazine.com/news/verizon-dbir-jump-vulnerability/
[4] L. Cardiet, “Living Off the Land (LOTL) Attacks: What Security Teams Must Know.” Accessed: Mar. 13, 2026. [Online]. Available: https://www.vectra.ai/topics/living-off-the-land
[5] “Website.” [Online]. Available: https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-038a
[6] “Picus Threat Library Updated for Document Malware of the OilRig (APT34) Threat Group.” Accessed: Mar. 13, 2026. [Online]. Available: https://www.picussecurity.com/resource/blog/oilrig-apt


.png?width=353&height=200&name=Ni8mare-ET-preview-oct25%20(1).png)






