Key Takeaways
- Watering hole attacks compromise websites your employees already trust. Firewalls and email filters generally offer no protection.
- Attackers wait for victims to visit. Malware delivers silently, with zero user interaction required.
- The attack runs in four stages: reconnaissance, website compromise, payload delivery, and post-infection activity. Attackers often stay hidden for months.
- Nation-state groups like APT29 have used this technique against government websites as recently as 2024 and 2025.
- Defense requires layers: patch continuously, deploy EDR tools, use Secure Web Gateways, apply Zero Trust to web traffic, and train your users.
- Validate your controls with Picus Security Control Validation. It simulates the malware delivered through watering hole attacks against your live security controls. When a gap is found, it tells you exactly what to fix.
Imagine locking every door in your building. Then finding out attackers never tried the doors. They poisoned the coffee machine in the lobby instead.
That is essentially what a watering hole attack does. Instead of targeting your network directly, attackers compromise the websites your employees already trust and visit every day. Your firewall never sees it coming. Your email filters are useless. And by the time malware reaches your endpoint, the breach has already begun.
This attack technique has been used to hit government agencies and critical infrastructure operators. It's favored by some of the world's most sophisticated threat actors, including nation-state APT groups.
In this blog we will explain what you need to know about watering hole attacks, and more importantly, what you can do about them.
What Is a Watering Hole Attack?
A watering hole attack is a cyberattack strategy where an adversary identifies websites frequently visited by a specific target group, compromises those websites with malicious code, and waits for victims to become infected simply by browsing. The attack exploits user trust in familiar, legitimate sites rather than relying on deceptive emails or direct network intrusion.
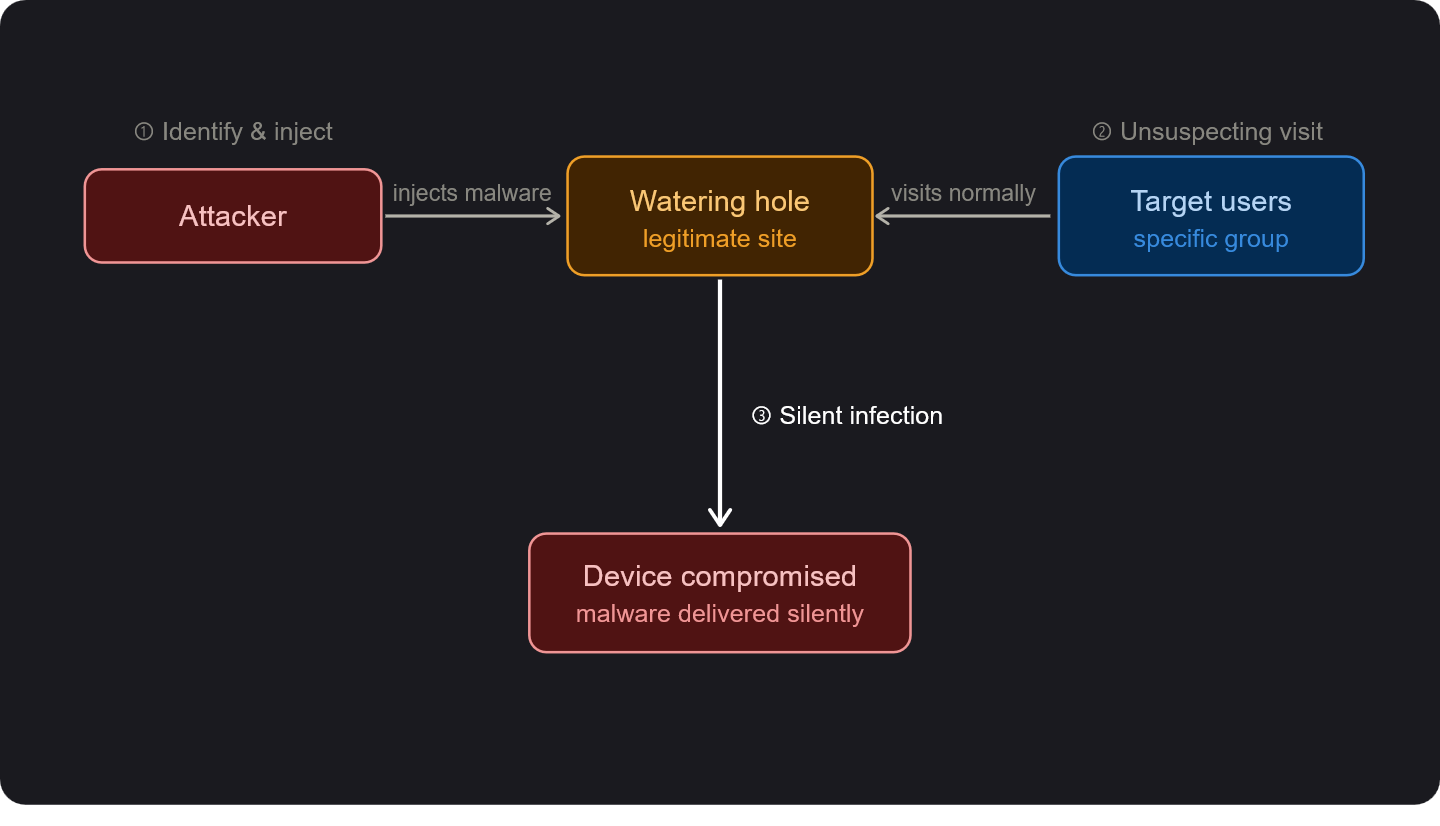
Figure 1. Illustration of a watering hole attack
The name comes from a nature analogy. Predators in the wild don't chase their prey. They wait patiently at the watering hole, knowing the prey will come to them eventually. The term was formally named in the RSA Blog in 2012 [1], but the tactic itself is older.
What makes this attack so dangerous is its use of legitimate sites. These attacks are executed via legitimate websites that cannot be easily blacklisted, and the malware used is often designed to avoid antivirus detection. Attackers will frequently target users from specific IP address ranges, making the attack invisible to others.
Watering hole attacks differ from phishing in one key way. Phishing goes out to the victim. Watering hole attacks wait for the victim to arrive. That shift in direction makes them significantly harder to detect with perimeter defenses.
How Does A Watering Hole Attack Work?
A watering hole attack follows a clear kill chain: profile the target → identify frequently visited websites → compromise one or more of those sites → then wait. In this chain, the malware is usually delivered via drive-by download, meaning the victim never clicks anything suspicious.
Here is what happens at each stage:
Stage 1: Reconnaissance
Attackers begin by studying their target, whether that is a specific company, government agency, or industry sector. They map out which websites employees frequent. This might include industry news portals, professional forums, regulatory body websites, or trade association pages.
Threat actors use a range of intelligence tools for this step, including search engines, social media, website demographic data, and sometimes spyware.
Stage 2: Website Compromise
Once a target website is selected, attackers look for vulnerabilities. Common methods include SQL injection, cross-site scripting (XSS), zero-day exploits in plugins or browsers, and compromised content delivery networks (CDN).
Attackers typically plant malicious code inside the site's HTML or JavaScript, which quietly redirects visitors toward a fake page designed to deliver malware.
Stage 3: Payload Delivery
When a visitor from the target group hits the compromised page, the malicious code activates.
In many cases, the malware downloads silently with no user interaction required, which is called a drive-by download. In others, social engineering prompts the user to run a file, such as a fake software update.
Stage 4: Post-Infection Activity
Once the malware is active, attackers can escalate privileges, move laterally through the network, steal credentials, and exfiltrate data. The stealthy nature of these attacks often allows threat actors to remain undetected for extended periods, sometimes months.
This is where the real damage compounds. By the time a breach is discovered, the attacker may have already mapped the internal network, harvested credentials, and established persistent access.
Real-World Watering Hole Attack Examples
Watering hole attacks are relatively rare compared to phishing, but they carry an exceptionally high success rate. The victims tend to be high-value targets in government, finance, defense and critical infrastructure.
Here are some of the real incidents caused by watering hole attacks:
Japan: University and Media Websites (2023)
JPCERT/CC confirmed two watering hole attacks targeting a Japanese university research laboratory and a media website in 2023. Both attacks used social engineering to trick visitors into executing malware disguised as legitimate software updates [3].
APT29 and the Mongolian Government Websites (2023-2024)
Between November 2023 and July 2024, the Russian-linked APT29 group (also known as Cozy Bear) compromised multiple Mongolian government websites and used them to deploy spyware targeting visitors with vulnerable iOS and Android devices [2].
SilentSelfie: Kurdish Community Websites (2024)
In 2024, a watering hole campaign dubbed SilentSelfie compromised 25 websites linked to the Kurdish minority. The attack deployed four distinct variants, ranging from stealing user location data to installing malicious Android applications [4].
This incident showed how watering hole attacks can be used for politically motivated surveillance at scale.
EmEditor Download Page Compromise (December 2025)
In late December 2025, EmEditor, a widely used text and code editor, published a security advisory warning users that its official download page had been compromised. The attackers' goal was to distribute a trojanized version of the software to unsuspecting users.
EmEditor has longstanding recognition within Japanese developer communities, suggesting the attackers were specifically targeting that user base [5].
What Can You Do To Prevent Such Attacks?
Preventing watering hole attacks requires a layered security approach that combines technical controls, continuous monitoring, and regular validation of your defenses. No single tool stops every attack.
Here are the most effective prevention measures:
Patch and Update Continuously
Keeping software, browsers, and plugins up to date removes the known vulnerabilities that watering hole attacks most commonly exploit.
Zero-day exploits are harder to defend against, but many real-world watering hole attacks use vulnerabilities that have been public for weeks or months. Delayed patching is one of the biggest risk multipliers.
Deploy Advanced Threat Protection
Standard antivirus will not catch zero-day exploits or novel malware variants. Organizations need behavioral analysis tools that can detect suspicious activity at the endpoint level, even when the malware itself has never been seen before.
EDR (Endpoint Detection and Response) solutions are particularly valuable here, as they monitor device behavior continuously rather than just scanning for known signatures.
Use Secure Web Gateways
Secure Web Gateways (SWGs) provide application control, URL filtering, data loss prevention, and deep HTTPS inspection. They can identify and block traffic to compromised websites before the malicious payload reaches the endpoint. Coupled with browser isolation, this significantly limits the blast radius of a watering hole compromise.
Apply a Zero Trust Model to Web Traffic
Watering hole attacks succeed partly because employees trust certain websites by default. All third-party traffic should be treated as untrusted until verified, regardless of whether it comes from a partner site or a familiar internet property.
Zero trust architecture limits the ability of attackers to move laterally even if an initial infection occurs.
Train Your People
Users who understand what a watering hole attack looks like can recognize early warning signs, such as unusual pop-ups on trusted sites, unexpected download prompts, or sudden site maintenance notices.
User education significantly reduces dwell time by shortening the time between infection and detection.
Validate Your Controls Regularly
Every prevention measure in the world means nothing if your controls don't catch the malware once it lands. If a watering hole attack does infect a device on your network, your endpoint protection, detection rules, and response workflows need to kick in immediately. A misconfigured tool or an outdated signature can let malware run silently for weeks.
This is where Breach and Attack Simulation (BAS) becomes critical. BAS tests whether your controls would actually detect and block the malware downloaded during a watering hole attack, before a real attacker finds out they won't.
How to Validate Your Defenses Against Watering Hole Attacks
Knowing your defenses are in place is not the same as knowing they work. A watering hole attack can drop malware onto a device without any user interaction. When that happens, your security controls need to detect it, block it, and respond to it automatically.
This is exactly what Picus Security Control Validation (SCV), powered by Breach and Attack Simulation (BAS), is built for. It continuously simulates the malware and techniques used in watering hole attacks against your live controls, including drive-by download payloads, post-compromise behaviors like lateral movement and data exfiltration. You don't have to wait for a real attack to find out if your stack responds correctly.
The simulations are powered by the Picus Threat Library, maintained by Picus Labs. It contains thousands of real-world threat samples and techniques mapped to MITRE ATT&CK, updated continuously to reflect the latest attacker behaviors, including newly observed watering hole campaigns.
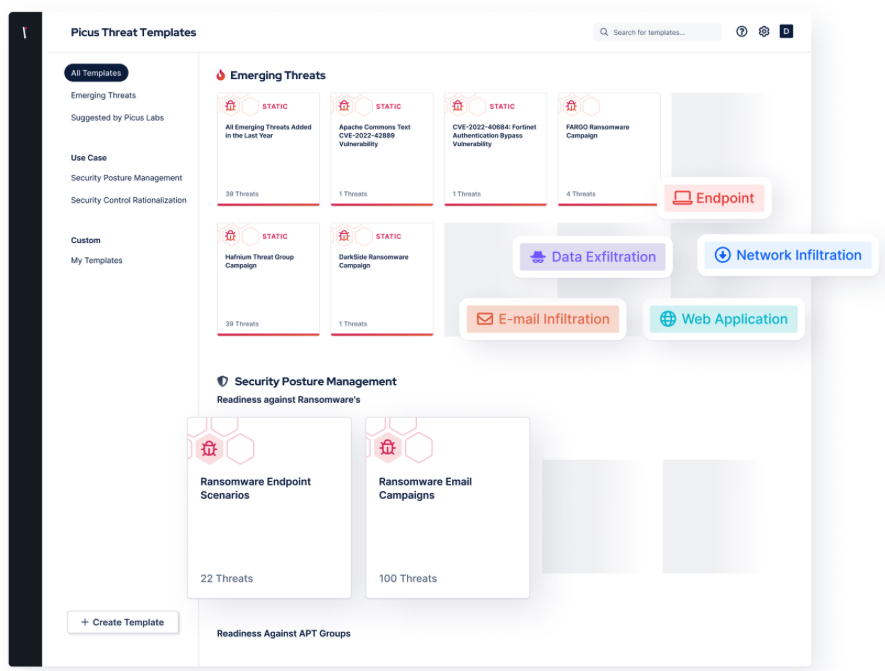
Figure 2. Picus Threat Library, Emerging Threats Templates
When a gap is found, the Picus Mitigation Library steps in. It provides vendor-specific, actionable recommendations mapped to your exact security tools, so your team knows precisely which rule to update, which signature to enable, or which configuration to fix.
Watering hole attacks don't announce themselves. But with continuous validation, your team doesn't have to wait for one to find out if your controls are ready. You test, you fix, you retest. The gaps close before attackers can reach them.
Request a demo and see how Picus exposes the gaps a watering hole attack would exploit in your current stack.
References
[1] W. Gragido, “Speaking of Security – The RSA Blog and Podcast,” Speaking of Security - The RSA Blog and Podcast. Accessed: Mar. 15, 2026. [Online]. Available: https://web.archive.org/web/20121212050809/http://blogs.rsa.com/lions-at-the-watering-hole-the-voho-affair/
[2] C. Lecigne, “State-backed attackers and commercial surveillance vendors repeatedly use the same exploits,” Google. Accessed: Mar. 16, 2026. [Online]. Available: https://blog.google/threat-analysis-group/state-backed-attackers-and-commercial-surveillance-vendors-repeatedly-use-the-same-exploits/
[3] “Recent Cases of Watering Hole Attacks, Part 1 - JPCERT/CC Eyes,” JPCERT/CC Eyes. Accessed: Mar. 16, 2026. [Online]. Available: https://blogs.jpcert.or.jp/en/2024/12/watering_hole_attack_part1.html
[4] The Hacker News, “Watering Hole Attack on Kurdish Sites Distributing Malicious APKs and Spyware,” The Hacker News. Accessed: Mar. 16, 2026. [Online]. Available: http://thehackernews.com/2024/09/watering-hole-attack-on-kurdish-sites.html
[5] “Watering Hole Attack Targets EmEditor Users With Information-Stealing Malware,” Trend Micro. Accessed: Mar. 16, 2026. [Online]. Available: https://www.trendmicro.com/tr_tr/research/26/a/watering-hole-attack-targets-emeditor-users.html


.png?width=353&height=200&name=Ni8mare-ET-preview-oct25%20(1).png)






