Key Takeaways
- Data exfiltration prevention rates dropped from 9% to just 3%, meaning 97 out of 100 exfiltration attempts go unblocked.
- Attackers follow a four-step process: gaining initial access, moving laterally across the network, staging and compressing data, and transferring it out using protocols like DNS and HTTPS or cloud services like Google Drive and Dropbox.
- Data exfiltration, data leakage, and data breach are distinct. Exfiltration is deliberate and attacker-driven. Leakage is accidental. A breach is any unauthorized access to protected data.
- 45% of data breaches are caused by insider threats, making internal monitoring as critical as perimeter defense.
- The average cost of a ransomware or extortion attack is $5.08 million per incident. Healthcare breaches average $7.42 million per incident.
- Picus Security Control Validation uses Breach and Attack Simulation (BAS) to continuously test your defenses against real exfiltration techniques and identify gaps in your security stack.
Data exfiltration is perhaps the most damaging and hardest-to-detect segment of a cyber attack. According to Picus Security's Blue Report 2025, data exfiltration prevention rates collapsed from 9% to just 3%. That means 97 out of every 100 exfiltration attempts go unblocked.
As your team is busy fighting ransomware and patching vulnerabilities, attackers are busily exfiltrating your most sensitive data from your network. This guide will tell you exactly what data exfiltration is, how attackers exfiltrate data, and what your organization needs to do to stop data exfiltration.
What Are Data Exfiltration Attacks?
Data exfiltration attacks are targeted operations where an attacker steals critical data from an organization and moves it to an external location under their control. Unlike unintentional data disclosure (or leakage), this type of attack involves planning.
These attacks follow a clear pattern: gain access to the system, locate the critical data to be exfiltrated, and then exfiltrate the critical data undetected.
The MITRE ATT&CK framework recognizes data exfiltration as a distinct tactic (TA0010) with over 15 techniques used by real-world attackers to exfiltrate critical data from target systems.
The reason why data exfiltration attacks are so dangerous is their undetected nature. By the time an organization detects a data exfiltration attack, the attacker would have left weeks ago. The damage to an organization due to a successful data exfiltration attack, in terms of regulatory and legal ramifications and reputation damage, would outlast the entire process of handling the situation.
How Does Data Exfiltration Happen?
Attackers don't just walk in and take the information. They follow a methodical procedure, one designed to avoid being seen.
Figure 1. Steps of Data Exfiltration Attacks
Step 1: Initial Access
Threat actors use phishing emails, credential theft, and vulnerability exploitation attacks to breach the network.
Credentials theft is particularly dangerous as it lets attackers move freely inside your environment without triggering alerts.
Step 2: Discovery and Lateral Movement
Threat actors use the compromised credentials to move around the network and locate the high-value information.
They use this information to escalate their privileges and move around the network undetected. This step is silent.
Step 3: Staging and Compression
Attackers compress and encrypt the target data to reduce its size and avoid detection by Data Loss Prevention (DLP) tools.They prepare it for transfer in a way that looks like normal traffic.
Commonly used tools for this purpose are 7-Zip and WinRAR for compressing data. The attacker may also use built-in operating system tools such as tar for Linux or PowerShell's Compress-Archive for Windows, precisely because these tools are known to cause no alarms.
Step 4: Transfer
This is the last step where the attackers transfer the exfiltrated data out of the network.
They use various tools for the transfer, including HTTP and DNS protocols. They may also use cloud storage tools such as Google Drive and Dropbox.
Common Data Exfiltration Techniques and Attack Vectors
Attackers use a variety of methods for exfiltration. Here are the common techniques they use:
Exfiltration Over C2 Channels
In this technique, attackers transmit stolen information over the same communication channel used for communication with the malware.
This technique is difficult to detect because the communication already exists.
Exfiltration Over Alternative Protocols
Threat actors also exfiltrate data through different protocols, which include DNS, FTP, SMTP, and SMB.
This is also a difficult technique for a defender to detect, particularly for exfiltration that is done through the DNS protocol, since this data is not usually subjected to any kind of examination.
Exfiltration Over Web Services
In this case, attackers exfiltrate stolen information by uploading it to cloud storage services such as Google Drive, Dropbox, GitHub, or AWS S3.
The advantage of this method is that most firewalls allow traffic to these services by default. This is now standard practice by ransomware actors.
Insider Threats
In this case, an insider threat is a person within an organization who has access and uses it to exfiltrate stolen information.
An industry research conducted in 2025 indicated that 45% of data breaches are caused by insider threats [1], which is a clear indicator of how critical it is for your organization to monitor your network for insider threats.
Automated Exfiltration
Most modern malware has this capability, whereby attackers exfiltrate data through a process that is automated.
This method has also been documented by MITRE T1020, which has recorded this technique being used by attackers for mass data exfiltration.
Steganography and Obfuscation
This is a method whereby attackers hide data within image files, videos, and other types of data that are not likely to be detected by a data loss prevention system.
Data Exfiltration vs. Data Leakage vs. Data Breach
Data exfiltration, data leakage, and data breach are not synonymous. Understanding the differences between them will enable you to build the right defense against each of them.
Data exfiltration is a deliberate and adversarial act. In this case, an attacker is working to steal your data.
On the other hand, data leakage is an unintentional act. It involves the leaking of sensitive information due to a misconfigured cloud storage bucket, sending sensitive information to the wrong person via email, or sharing files insecurely. In this case, no attacker is required to perform the act.
A data breach is a general term. It encompasses any incident where unauthorized entities access sensitive information. To illustrate this, consider the following analogy. All data exfiltrations are data breaches. However, not all data breaches are exfiltrations.
Below table explains the differences:
|
Intent |
Actor |
Outcome |
|
|
Data exfiltration |
Deliberate |
External attacker or malicious insider |
Data stolen and transmitted externally |
|
Data leakage |
Accidental |
Employee mistake or misconfiguration |
Data exposed without transfer |
|
Data breach |
Either |
Either |
Unauthorized access to protected data |
The Cost of Data Exfiltration
The cost of data exfiltration is substantial.
The Red Report 2026 from Picus Security revealed a drop of 38% in encryption-based attacks in the last 12 months, as more attackers are using exfiltration-based attacks. The rise of exfiltration-based attacks, replacing encryption-based attacks, is increasing breach lifecycle times.
According to IBM, in its most recent 2025 Cost of a Data Breach Report [2], the cost of an extortion/ransomware attack averages out to be $5.08 million per incident.
Healthcare is the hardest hit by data exfiltration. The current average cost of a data breach in the healthcare industry stands at $7.42 million per incident, which is down from the pandemic-related peaks but remains the most costly sector to attack, given the strict regulatory requirements and the value of data on the black market.
Data sprawls and exfiltration continue to significantly extend the breach lifecycle. Breaches of unmanaged and sprawled-out data across various environments have an average of 276 days to detect and contain. The longer undetected, the longer breach costs for you.
How to Prevent Data Exfiltration
The prevention of data exfiltration requires ongoing testing of your controls for effectiveness against these techniques. Having one tool does not prevent exfiltration from your network.
Here are a few critical strategies to add to your data exfiltration prevention checklist:
- Implement and validate DLP tools: These tools monitor and prevent unauthorized data exfiltration. The configuration of these tools can change because of policy, exceptions, and system updates. Test for exfiltration attempts. Test for both clear text and for attempts using different formats like PDF, CSV, and DOCX.
- Implement Zero Trust and Least Privilege: Limiting access based on roles is critical. A breached account should have limits on their movement and reach. Limiting their privileges can prevent further damage. Reevaluate their access regularly.
- Monitor for exfiltration attempts: Outbound traffic should be monitored for suspicious activity. DNS, HTTPS, and cloud storage should be monitored. Large volumes of data sent to new destinations are indicators of exfiltration.
- Map your coverage using MITRE ATT&CK: This framework contains fifteen different exfiltration techniques. Mapping your coverage is critical. You can prioritize remediation based on known attacker behaviors.
- Detect behavioral anomalies: Behavioral analytics can identify suspicious activity. Massive data exfiltrations during off-hours require immediate flagging, not detection weeks later during a log review.
How to Validate Your Defenses Against Data Exfiltration Attacks
Picus Security Control Validation, powered by Breach and Attack Simulation (BAS), continuously and safely tests the effectiveness of an organization's security tools by emulating real-world adversary behaviors, including those found in the Data Exfiltration Attacks module.
This particular module allows an organization to safely simulate attacks against their security stack, such as a DOC(X) Format Data Exfiltration Campaign or the theft of sensitive regional PCI and PII information.
This is done by utilizing the Picus Threat Library, a vast and dynamic library of attacks from adversaries around the world, which is constantly being updated with the latest threat intelligence by the research and development division at Picus Labs. 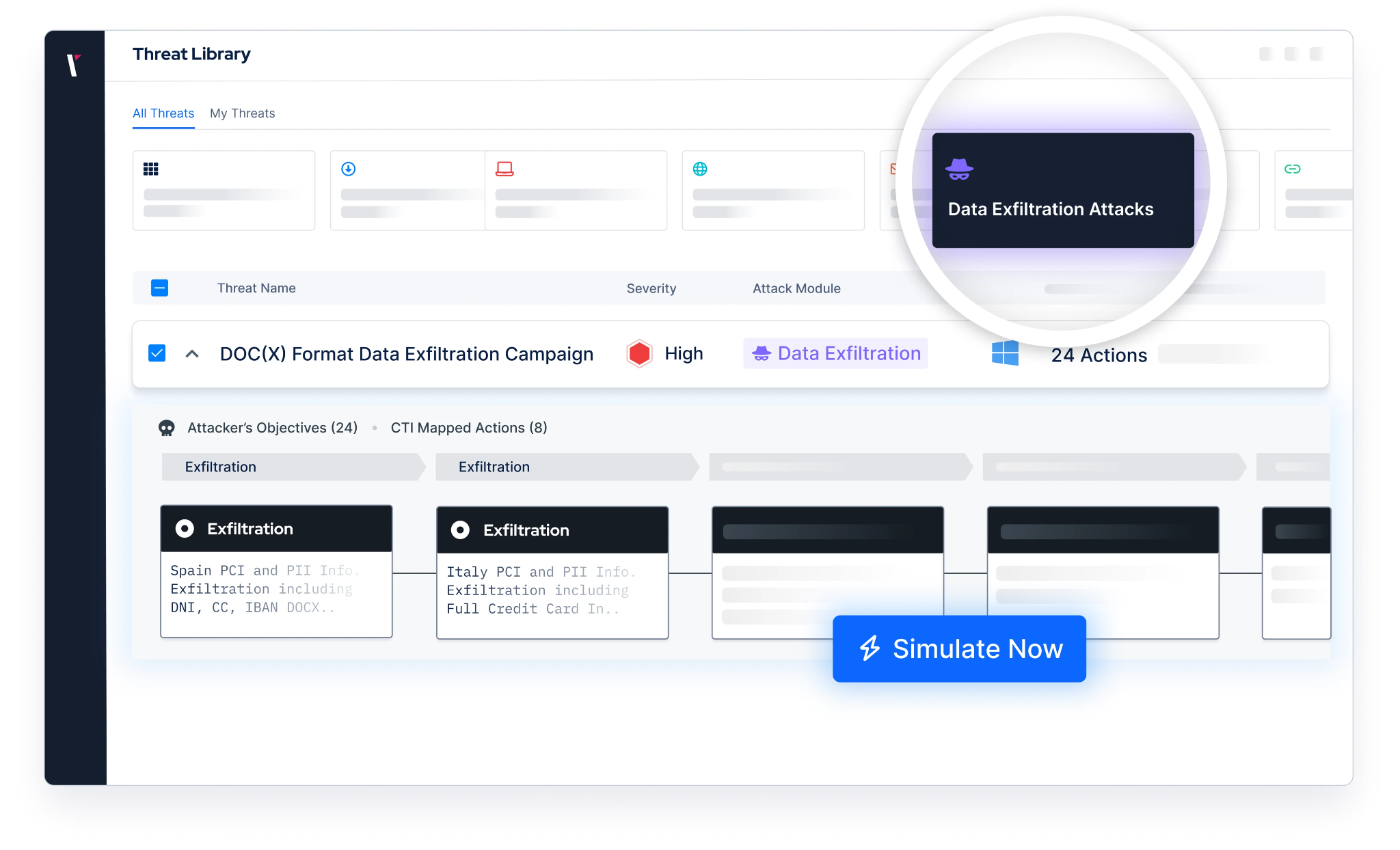
Figure 2. Picus Threat Library, Data Exfiltration Attacks Module
Request a demo and see how Picus exposes the gaps a data exfiltration attack would exploit in your current stack.
References
[1] P. Spencer, “Hidden Enemy Within: Decoding the 2025 Ponemon Institute Report on Insider Threats,” Kiteworks | Your Private Data Network. Accessed: Mar. 25, 2026. [Online]. Available: https://www.kiteworks.com/cybersecurity-risk-management/hidden-enemy-within-decoding-the-2025-ponemon-institute-report-on-insider-threats/
[2] “[No title].” Accessed: Mar. 25, 2026. [Online]. Available: https://www.ibm.com/downloads/documents/us-en/131cf87b20b31c91



.png?width=353&height=200&name=Ni8mare-ET-preview-oct25%20(1).png)





