Meeting Bank Negara Malaysia's RMiT Requirements with Picus
| March 16, 2026
Executive Summary
The Risk Management in Technology (RMiT) policy document, issued by Bank Negara Malaysia (BNM) on 28 November 2025, sets out the minimum requirements for financial institutions to manage technology risk, including cyber risk, across Malaysia's financial sector. Applicable to licensed banks, insurers, takaful operators, payment system operators, e-money issuers, and more, RMiT reflects BNM's expectation that financial institutions do not merely document their security posture. They must demonstrate it.
While the regulatory intent of RMiT is clear, the operational challenge is not.
Compliance is no longer satisfied by publishing policies, configuring controls, or completing point-in-time assessments alone. Financial institutions are now expected to prove that cybersecurity controls operate effectively under real attack conditions, and to do so continuously.
Across governance, technology risk management, cybersecurity operations, and digital services domains, RMiT shifts expectations from control presence to control effectiveness. This creates a growing need for defensible, repeatable, and current evidence that controls work as intended in real-world environments.
This is where the Picus Platform changes how RMiT compliance is achieved. By continuously validating security controls against real adversary behavior, Picus turns technical control performance into operational, audit-ready evidence, enabling financial institutions to meet RMiT requirements with confidence.
Showing RMiT Compliance with Evidence
RMiT was designed to reduce risk by emphasizing continuous monitoring, proactive detection, and cyber resilience. Operationalizing that intent requires continuous validation.
Modern financial institution environments rely on security controls across identity, endpoint, network, detection, cloud, and OT layers to enforce RMiT requirements. Picus approaches compliance by validating these controls directly.
Instead of asking whether a control is configured, Picus tests whether it:
- Blocks real attack techniques
- Detects adversary behavior
- Triggers alerts and investigations
- Supports response and recovery actions
This shifts RMiT compliance from policy-driven assertions to evidence-based assurance, where effectiveness is demonstrated continuously rather than inferred periodically.
How Picus Supports Key RMiT Requirements
RMiT Section 11.6: Red Team Simulation
"A financial institution must conduct a realistic 'Red Team' simulation attack on its infrastructure at least once every three years to proactively identify and manage potential vulnerabilities." (Section 11.6)
How Picus supports this requirement
Section 11.6 requires financial institutions to conduct realistic red team simulations to proactively identify and manage vulnerabilities across their infrastructure.
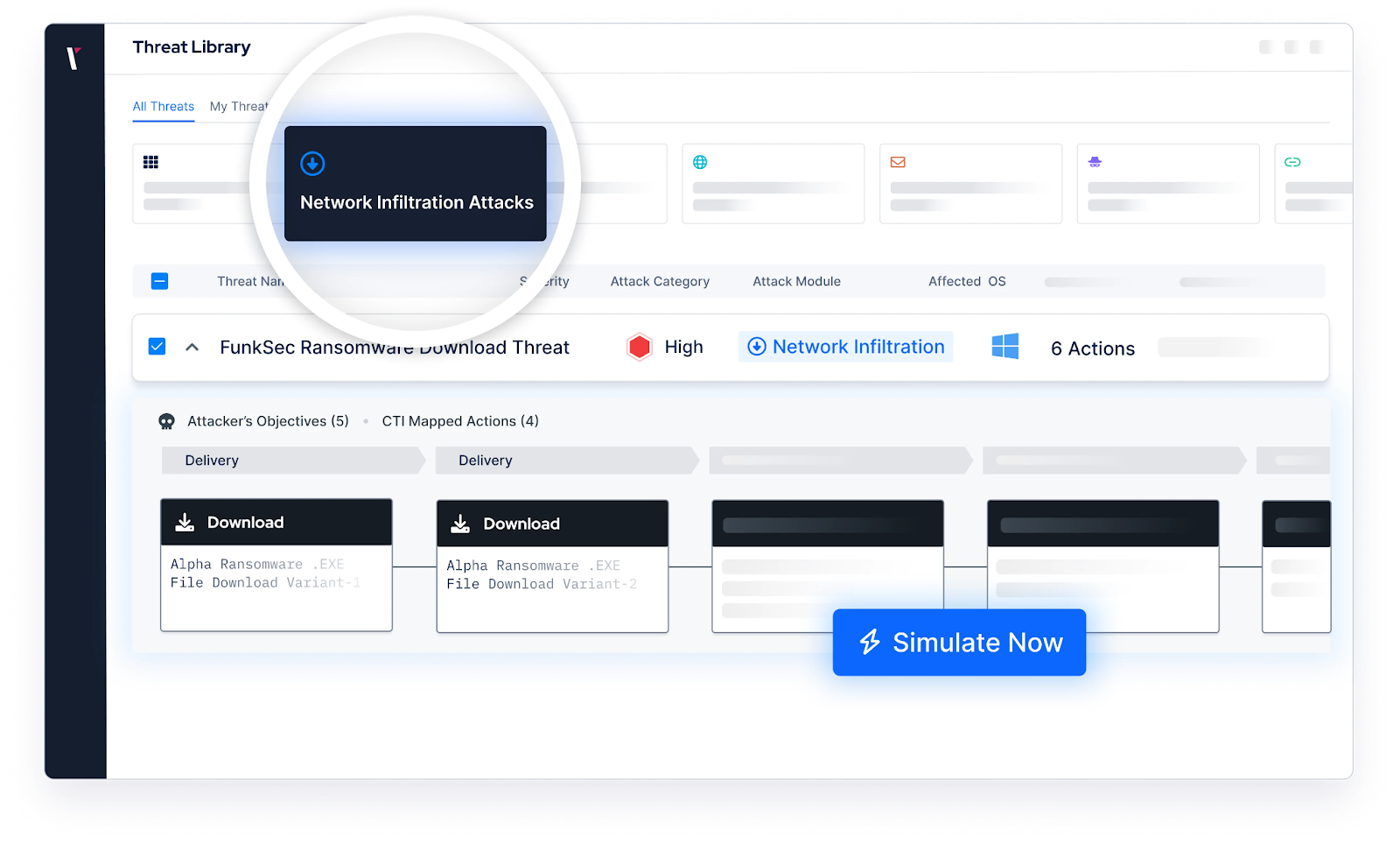
Picus supports this requirement by continuously executing adversary-emulated attack techniques aligned with real-world TTPs, covering the full cyber-attack lifecycle from reconnaissance through to data exfiltration. This allows organizations to validate control effectiveness between mandated simulations and produce evidence that cybersecurity measures operate effectively against prevalent threats, ensuring they enter every formal red team engagement with a validated, defensible baseline.
RMiT Appendix 5, Part D: Vulnerability Assessment and Penetration Testing (VAPT)
"A financial institution must perform a quarterly vulnerability assessment of external and internal network components that support all critical systems." (Appendix 5, Part D, Paragraph 2)
"A financial institution must conduct annual intelligence-led penetration tests on its internal and external network infrastructure, critical systems as well as digital services including web, mobile and all external-facing applications."(Appendix 5, Part D, Paragraph 3)
"A financial institution must undertake an independent compromise assessment on the technology infrastructure of its critical systems at least once every three years." (Appendix 5, Part D, Paragraph 6)
How Picus supports this requirement
Appendix 5, Part D mandates quarterly vulnerability assessments, annual intelligence-led penetration tests, and triennial compromise assessments.
This requirement is likely to impose a significant, recurring operational burden on security teams. To help reduce this operational burden, Picus complements these mandatory exercises by automating repeatable attack scenarios that continuously validate baseline security controls between formal engagements.
By simulating real attack paths across the network, endpoint, web application, email, cloud, and data layers, Picus helps organizations prioritize remediation based on real exploitability rather than theoretical severity alone. Hence, this reduces manual effort, expanding coverage, and enabling human testers to focus on advanced and creative attack paths during formal engagements.
RMiT Appendix 5, Part A: Network Security
"A financial institution must ensure technology networks are segregated into multiple zones according to threat profile. Each zone shall be adequately protected by various security devices including but not limited to firewall and Intrusion Prevention System (IPS)." (Appendix 5, Part A, Paragraph 1)
How Picus supports this requirement
Appendix 5, Part A requires financial institutions to implement layered network security controls across all zones, including perimeter defenses, endpoint protection, and controls for remote access and server-to-server connections.
Picus supports this requirement by continuously simulating attack techniques across network layers, validating whether firewalls, IPS, and other perimeter and internal controls effectively detect and block adversary behavior as configured.
By testing real-world attack traffic against each network zone, Picus enables security teams to identify misconfigured controls, undetected lateral movement paths, and gaps in segmentation before adversaries can exploit them. The results provide continuous, evidence-based assurance that the network security controls required under Appendix 5, Part A are operating effectively in practice.
RMiT Section 11.2 & 11.3: Cyber Resilience Framework (CRF)
"A financial institution must develop a CRF which clearly articulates its governance for managing cyber risks, its cyber resilience objectives and its risk tolerance... The framework must be able to support the effective identification, protection, detection, response, and recovery (IPDRR) of systems and data..." (Section 11.2)
"...identification of cybersecurity threats, vulnerabilities and countermeasures to secure digital services delivery against cyber-attacks..." (Section 11.3(c))
How Picus supports this requirement
Sections 11.2 and 11.3 require financial institutions to build a Cyber Resilience Framework that spans identification, protection, detection, response, and recovery across all systems and data.
Picus supports every phase of this IPDRR model by validating whether controls across each layer of their multi-layered defense structure actually perform as intended. Rather than relying on assumed control effectiveness, Picus produces continuous, evidence-based validation data that directly feed the CRF, enabling financial institutions to demonstrate that their resilience objectives are met in practice, not just on paper.
RMiT Section 11.9 & Appendix 5, Part C: Security Operations Centre (SOC) and Continuous Monitoring
"A financial institution must ensure continuous and proactive monitoring and timely detection of anomalous activities in its technology infrastructure to prevent potential compromise of its security controls or weakening of its security posture." (Section 11.9)
"A financial institution must ensure its SOC has adequate capabilities for proactive monitoring of its technology security posture... detect anomalous user or network activities, flag potential breaches and establish the appropriate response." (Appendix 5, Part C, Paragraph 1)
How Picus supports this requirement
Bank Negara Malaysia’s (BNM) RMiT mandates that SOC capabilities go beyond passive log collection; they must actively detect anomalous behavior, flag potential breaches, and support timely response.
Picus supports this requirement by executing real-world attack scenarios and analyzing detection outcomes. Using Picus Detection Analytics, organizations can determine which attack behaviors are prevented, if not, whether they are properly logged, trigger alerts, and identify visibility gaps across their SOC stack.
This supports continuous review and tuning of detection mechanisms, SIEM use cases, and monitoring coverage, ensuring the SOC remains effective against evolving adversary techniques.
RMiT Section 11.10: Cyber Threat Intelligence
"A financial institution must establish a process to collect, analyse and evaluate cyber threat information in relation to its environment ('cyber threat intelligence') to promptly detect cyber threats, including data breach incidents and spread of misleading information..." (Section 11.10)
How Picus supports this requirement
Section 11.10 requires financial institutions to operationalize threat intelligence, not merely collect it.
Picus supports this requirement by converting threat intelligence reports into executable validation tests. Picus Labs continuously updates the Picus Threat Library with newly observed TTPs and adversary techniques, with a mean time to release of just 5.3 hours and a guaranteed SLA of 24 hours for emerging threats such as CISA alerts.
This allows financial institutions to verify that controls implemented in response to threat intelligence actually mitigate the identified threats, closing the gap between intelligence consumption and operational defense.
RMiT Section 11.12 & 11.13: Cyber Crisis Management and Incident Response (CIRP)
"A financial institution must establish comprehensive cyber crisis management policies and procedures that incorporate cyber-attack scenarios and responses..." (Section 11.12)
"A financial institution must establish and implement a comprehensive Cyber Incident Response Plan (CIRP)..."(Section 11.13)
How Picus supports this requirement
Sections 11.12 and 11.13 require financial institutions to maintain a CIRP that is actionable, tested, and ready to invoke across the full incident lifecycle, from detection and containment through to recovery and post-incident review.
Picus supports this requirement by safely simulating attacks that exercise detection, escalation, and containment workflows in live environments, allowing organizations to validate whether incident response processes would function as required under real attack conditions.
The output serves as defensible evidence that the CIRP has been tested against realistic threat scenarios.
RMiT Section 11.16: Annual Cyber Drill Exercise
"A financial institution must conduct an annual cyber drill exercise to test the effectiveness of its CIRP including the out-of-band communication methods, based on various current and emerging threat scenarios (e.g. social engineering), with the involvement of key stakeholders including members of the board, senior management and relevant third party service providers." (Section 11.16)
How Picus supports this requirement
Section 11.16 mandates recurring, scenario-based cyber drill exercises that test people, process, and technology together.
icus supports this requirement by embedding adversarial simulations into operational environments, enabling continuous and realistic exercises between annual drills. By providing realistic attack scenarios aligned with known and emerging threat intelligence, including malware, Advanced Persistent Threat (APT), and CVE exploitation campaigns observed in the wild, Picus ensures that annual exercises are grounded in validated, evidence-based findings, and that the gaps they uncover have already been identified and tracked throughout the year.
RMiT Section 10.17 & 10.18: Patch and End-of-Life System Management
"A financial institution must ensure that all systems including digital services are not running with known security vulnerabilities, on outdated platform or end-of-life (EOL) technology systems." (Section 10.17)
"A financial institution must establish a patch and EOL management framework which addresses... identification and risk assessment of all technology assets for potential vulnerabilities arising from undeployed patches or EOL systems... formulation of criteria, priority and turnaround time for patch deployment according to the severity of the vulnerabilities identified." (Section 10.18)
How Picus supports this requirement
Sections 10.17 and 10.18 require financial institutions not only to identify vulnerabilities but to prioritize and remediate them based on operational risk.
Picus supports this requirement through its Exposure Validation (EXV) capability, which tests vulnerabilities identified by scanners such as Tenable and Qualys to determine whether they are truly exploitable in the institution's specific environment.
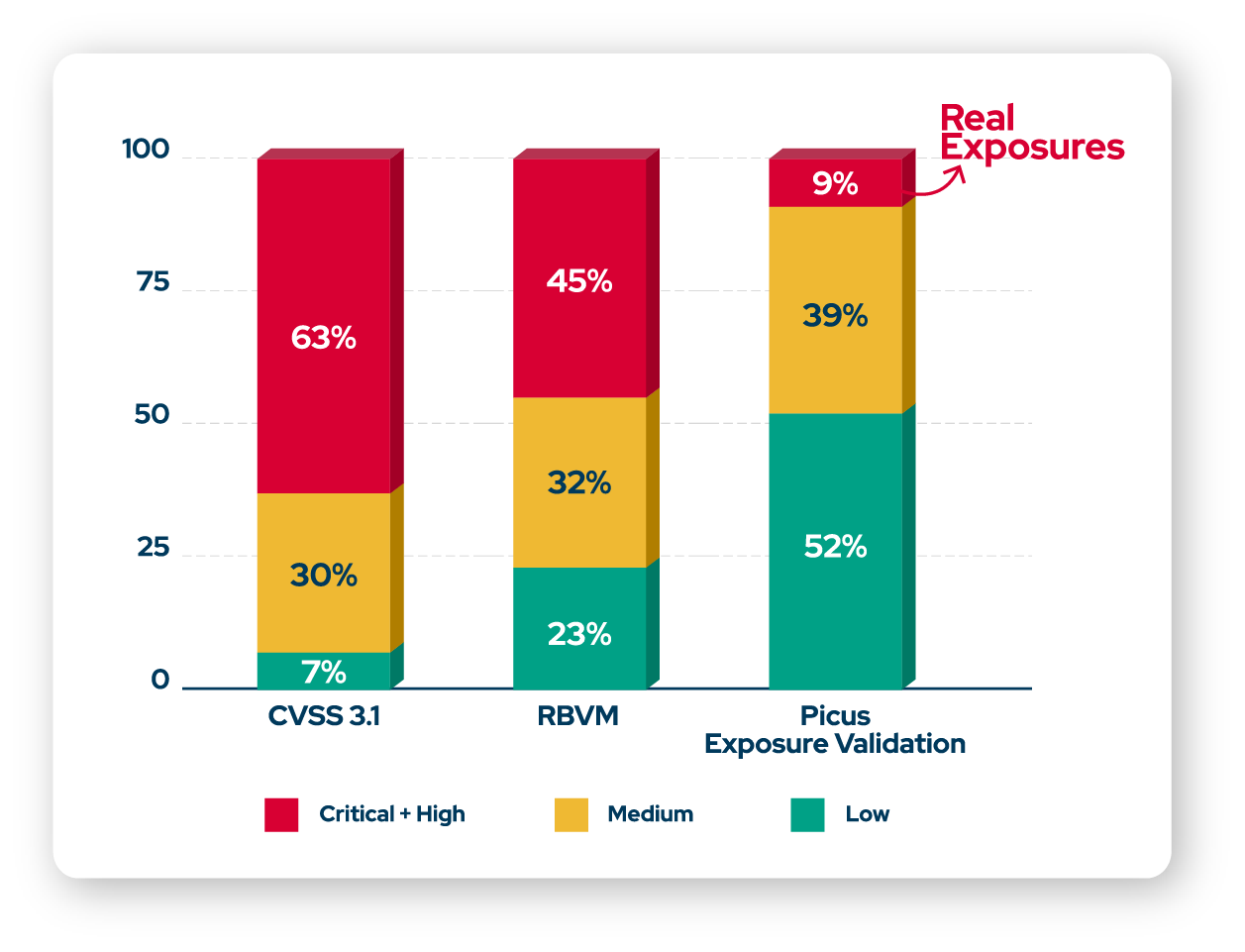
Figure 1. Identifying and remediating actual exploitable exposures with real risks using the Picus Platform.
By simulating real attack paths, Picus enables security teams to distinguish between theoretical vulnerabilities and those that represent genuine exposure, allowing patch prioritization decisions to be driven by validated risk rather than CVSS scores alone.
RMiT Section 9.1 & 9.2: Technology Risk Management Framework (TRMF)
"A financial institution must ensure that the TRMF is an integral part of the financial institution's enterprise risk management framework (ERM)." (Section 9.1)
"The TRMF must include... risk measurement and assessment approaches and methodologies... risk controls and mitigations... continuous monitoring to timely detect and address any material risks." (Section 9.2)
How Picus supports this requirement
Section 9.1 and 9.2 require financial institutions to embed technology risk management into their enterprise-wide ERM, with ongoing monitoring, risk measurement, and validated controls.
Picus supports this requirement by providing validated evidence of control effectiveness and real exposure, enabling risk registers and TRMF documentation to be updated with tested outcomes rather than assumptions. This improves risk prioritization decisions and ensures that the TRMF reflects the institution's actual security posture rather than a static, point-in-time view.
RMiT Section 8.1, 8.2 & 8.4: Board Governance and Oversight
"The board must establish and approve the technology risk appetite which is aligned with the financial institution's risk appetite statement." (Section 8.1)
"The board must... endorse and oversee the effective implementation of a sound and robust technology risk management framework (TRMF) and cyber resilience framework (CRF)..." (Section 8.2(b))
"The board must... allocate sufficient time to discuss cyber risks, including the strategic, reputational and liquidity risks and impact of operational disruption to stakeholders which could arise from an extreme cyber incident." (Section 8.4(b))
How Picus supports this requirement
RMiT places significant governance obligations on the board, requiring informed oversight of technology risk appetite, TRMF effectiveness, and cyber risk exposure.
Picus provides objective, continuously updated validation data, including the Picus Exposure Score (PXS) and MITRE ATT&CK-mapped coverage dashboards, that leadership can use to assess cybersecurity effectiveness in plain terms.
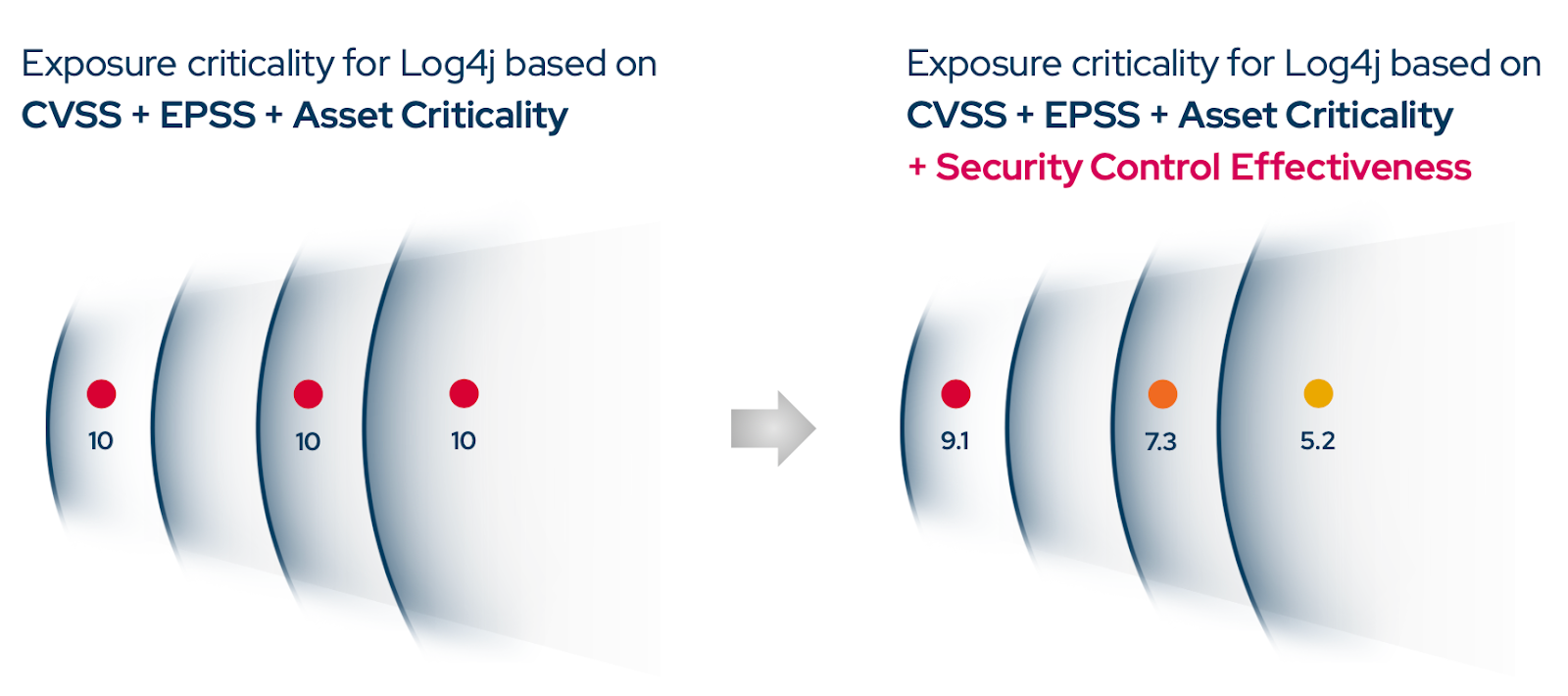
Figure 2. Picus Exposure Score introduces a level of granularity that allows teams to prioritize remediation based on evidence.
This supports evidence-based board oversight, enabling directors to fulfill their governance obligations with confidence rather than relying on assumption-based reporting.
RMiT Section 10.53 & 10.57: Access Control and User Activity Logging
"A financial institution must implement an access control policy for the identification, authentication, and authorisation of all users to its IT assets and data." (Section 10.53)
"A financial institution must ensure... user activities in critical systems are logged for audit and investigations. Activity logs must be maintained for at least three years and regularly reviewed in a timely manner." (Section 10.57(c))
How Picus supports this requirement
Sections 10.53 and 10.57 require financial institutions to enforce access controls and maintain complete, usable activity logs for critical systems.
Picus supports this requirement by validating whether real attack activity, including identity-based attacks such as credential abuse, privilege escalation, and lateral movement, is correctly detected, logged, and alerted by existing controls. This helps institutions confirm that logging mechanisms generate sufficient evidence to support investigations, audits, and regulatory requests, and that access control policies enforce the expected boundaries under realistic attack conditions.
RMiT Appendix 5, Part B: Data Security and Data Loss Prevention (DLP)
"A financial institution shall ensure that all data-at-rest of Personal Identifiable Information (PII) and transaction data are securely protected and rendered unreadable to unauthorised access through the implementation of robust encryption mechanisms or equivalent capabilities." (Appendix 5, Part B, Paragraph 1)
"A financial institution must design internal control procedures and implement appropriate technology in all applications and access points to enforce Data Loss Prevention (DLP) policies..." (Appendix 5, Part B, Paragraph 2)
How Picus supports this requirement
Appendix 5, Part B requires financial institutions to enforce data protection controls and DLP policies across data in use, in motion, and at rest.
Picus supports this requirement by simulating data exfiltration techniques across network, endpoint, and cloud layers, validating whether DLP controls, encryption enforcement, and perimeter defenses effectively prevent unauthorized data movement.
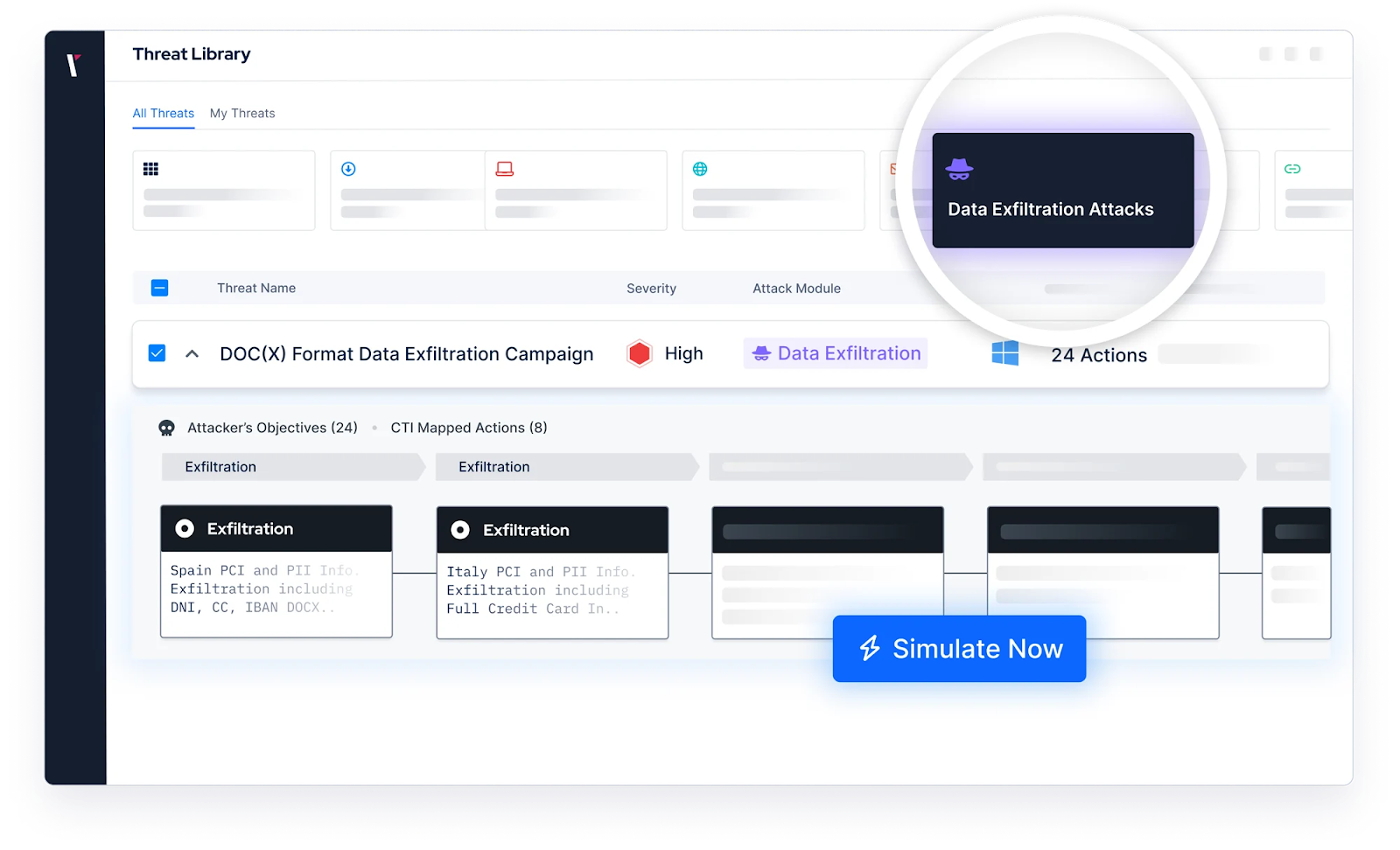
Figure 3. Testing the effectiveness of DLP solutions with Picus’ Security Control Validation (SCV) module
RMiT Appendix 10: Cloud Security Validation
"A financial institution should ensure integrated monitoring and full visibility of cloud services are established... continuous monitoring of system communications between the cloud service provider, on-premise IT systems and other service providers to ensure the security perimeter is not breached." (Appendix 10, Part B, Paragraph 10(b))
"A financial institution should proactively seek assurance of their cloud service providers to conduct periodic VAPT on the cloud infrastructure to ensure tenant isolation and overall security posture remains healthy." (Appendix 10, Part B, Paragraph 10(c))
How Picus supports this requirement
Appendix 10 mandates that financial institutions maintain continuous visibility and proactive security validation across their cloud environments.
Picus supports this requirement through its Cloud Security Validation (CSV) capability, which provides auditing and attack simulation across AWS, Azure, and GCP environments.
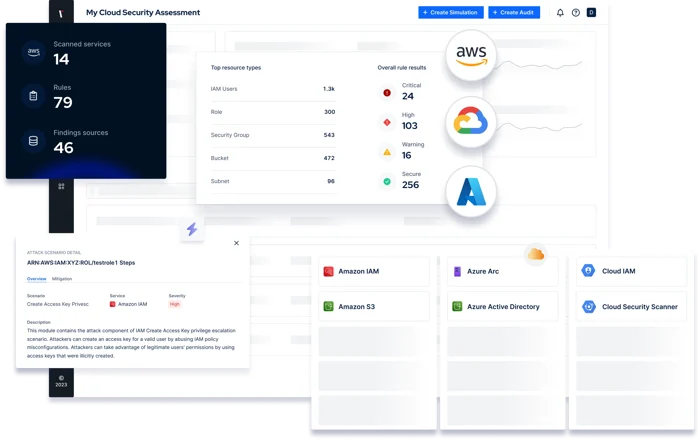
Figure 4. Picus’ Cloud Security Validation (CSV) being integrated within the Picus Platform
By simulating adversarial techniques targeting cloud infrastructure and cloud-to-on-premise boundaries, Picus helps financial institutions validate whether cloud segmentation, access controls, and monitoring mechanisms effectively prevent unauthorized access and lateral movement, without disrupting production operations.
RMiT Section 9.5: Policy Enforcement and Compliance Verification
"The CISO shall be responsible for ensuring that the financial institution's information assets and technologies are adequately protected, which includes... enforcing compliance with these policies, frameworks and other technology-related regulatory requirements." (Section 9.5(b))
How Picus supports this requirement
Bank Negara Malaysia’ RMiT places direct responsibility on the CISO to enforce compliance with policies and frameworks across the institution.
Picus validates whether controls enforcing those policies actually operate as expected in practice, helping CISOs identify and remediate gaps between documented policy and real-world execution. This provides the CISO with objective, continuous evidence to demonstrate compliance posture to both the board and regulators, supporting the accountability obligations defined under RMiT's governance structure.
RMiT Section 13.1: Technology Audits
"A financial institution must ensure that the scope, frequency, and intensity of technology audits are commensurate with the complexity, sophistication and criticality of technology systems and applications." (Section 13.1)
How Picus supports this requirement
Section 13.1 requires financial institutions to conduct technology audits at a depth and frequency that reflects the criticality and complexity of the systems being assessed.
Picus supports this requirement by providing continuously updated, evidence-based validation data that directly informs the scope and prioritization of technology audit activities. Rather than relying solely on point-in-time assessments, internal audit teams can leverage Picus findings, including MITRE ATT&CK-mapped control gaps, exposure scores, and remediation tracking, to ensure audit coverage is focused on areas of genuine, validated risk. This helps institutions demonstrate to auditors and regulators that the intensity of their audit activity is grounded in real control performance data, not assumptions.
Making RMiT Compliance Resilient with Validation
BNM's Risk Management in Technology (RMiT) aims to ensure that financial institutions remain operationally resilient because the controls protecting their technology environments work in practice.
Picus helps organizations move from periodic, assumption-based compliance to continuous, evidence-based assurance. By validating control effectiveness against real attack behavior, Picus turns RMiT compliance into a living, defensible security posture, one that satisfies BNM's expectations not just at the time of assessment, but continuously.
Get your demo and see how Picus helps financial institutions across Malaysia protect critical technology infrastructure with audit-ready evidence.









