BAS for Cyber Insurance: Prove Control Effectiveness and Lower Premiums
| March 18, 2026
The Underwriting Shift: Why Self-Attestation No Longer Works for Cyber Insurance Policies
Cyber insurance in 2026 is no longer a safety net. It is a qualifying test.
The days of simply checking "yes" on a self-attestation form and binding a policy are over. Insurers have been hit by years of devastatingly costly claims, and they have responded by fundamentally changing how they evaluate risk.
The numbers are stark.
- Coalition's 2026 Cyber Claims Report found that overall claims frequency rose 3% year-over-year in 2025, with initial ransom demands surging an incredible 47%.
- Ransomware remained the most expensive claim type, averaging $269,000 per incident.
- Meanwhile, business email compromise and funds transfer fraud together accounted for 58% of all cyber incidents observed.
- Looking at the broader fallout, the global average cost of a data breach reached $4.88 million in 2025, according to IBM, an all-time high.
These compounding losses have reshaped underwriting completely, making claim denials the new default.
According to a February 2026 NAIC report, nearly three times as many cyber insurance claims were closed without payment (28,555) as those that were paid (9,941). In excess cyber policies, unpaid claims outnumber paid ones by more than 20 to 1.
Industry data now puts claim rejection rates above 40%, with missing or undocumented security controls cited as a leading cause.
In one widely reported and sobering case, a municipality was denied an $18 million payout after a ransomware attack simply because multi-factor authentication (MFA) had not been fully implemented across all affected systems.
Why Security Controls Fail Cyber Insurance Requirements
The pattern behind these massive claim denials reveals a systemic gap: organizations are reporting what is deployed, not what is effective.
- A firewall is installed, but does it actually block the threats it should?
- EDR is running on every endpoint, but does it catch the specific evasion techniques attackers use today?
- SIEM rules are deployed, but do they actually fire when a real threat triggers them?
Insurers now scan public-facing assets, demand rigorous documentation (screenshots, policies, logs, proof of backup tests), and use AI-driven underwriting to build objective pictures of applicant risk profiles.
Carriers are increasingly moving from point-in-time assessments toward continuous telemetry feeds. Because of this deeper scrutiny, S&P Global Ratings forecasts a 15–20% increase in cyber insurance premiums in 2026, and Forrester predicts a 15% rise in global cyber premiums. This isn't just driven by more policies being written; it is driven by insurers demanding higher standards from policyholders.
The question underwriters now ask is not "Do you have these controls?" but "Can you prove they work?"
What BAS Measures for Cyber Insurance: Control Effectiveness, Not Just Control Presence
When an underwriter evaluates your risk, they are looking for documented proof of due care.
Breach and Attack Simulation (BAS) is the ultimate system of record for that proof. It continuously and safely simulates and emulates adversarial techniques, including ransomware payloads, lateral movement, and data exfiltration, to verify whether your specific security controls will actually stop what they're supposed to.
Though BAS tools can run CVE-based exploitation attacks, it doesn't necessarily perform chained vulnerability exploitation. Instead, it tests whether your security controls, firewalls, EDR, SIEM, WAF, and email gateways, are actually blocking, if not, properly logging and alerting on known threat behaviors.
The critical distinction is that BAS does not guess. It measures.
Unlike a vulnerability scanner that returns a theoretical list of CVEs ranked by a generic CVSS score, BAS answers the exact question the underwriter is asking: Do your actual security controls stop actual attack techniques? It executes real-world adversarial tactics, techniques, and procedures (TTPs) across the kill chain, and records exactly how every control in the path responds.
This evidence-based approach maps directly to what modern underwriters need, providing proof across five critical pillars:
- Prevention Control Effectiveness Scoring: BAS tests, including but not limited to, Next-Gen Firewalls (NGFW), Web Application Firewalls (WAFs), Intrusion Prevention Systems (IPS), Secure Email Gateways (SEG), and Data Loss Prevention (DLP) solutions against current threat intelligence and returns a measurable effectiveness percentage. You can tell an underwriter: "Our network prevention controls blocked 94% of simulated attack techniques across 3,200 tests in Q4."
- Detection and Alerting Rule Validation: Insurers require evidence that your detection, alerting and response capabilities (IDS, EDR, XDR, SIEM, other endpoint security tools, etc.,) actually function. BAS simulates threat behaviors and measures whether alerts are generated, transforming subjective claims into objective measurements.
- Continuous Risk Trending Over Time: Annual pentests give underwriters a single, rapidly aging snapshot. BAS runs continuously, producing month-over-month performance data that demonstrates a trajectory of continuous risk reduction.
- Closed-Loop Remediation Proof: Finding a gap is one thing; proving you closed it is another. Good ROI BAS platforms are expected to provide actionable remediation guidance, and after the fix is applied, automatically re-validate to confirm the gap is closed. This creates the auditable trail underwriters demand.
- Incident Response Readiness: Insurers view IR readiness as a primary factor in underwriting. BAS grounds tabletop exercises in real data, highlighting specific threat techniques (observed in real-life malware/threat group campaigns) that bypass current controls so you can build targeted, evidence-based response plans.
MITRE ATT&CK Coverage as Underwriting Evidence: What Insurers Actually Look For
The five pillars above describe what BAS measures. MITRE ATT&CK provides the common language for how those measurements are structured and communicated.
Underwriters increasingly work with technical advisors who need a standardized framework to assess defensive coverage. ATT&CK has become that framework, cataloging adversarial TTPs into a structured matrix that maps the full attack lifecycle.
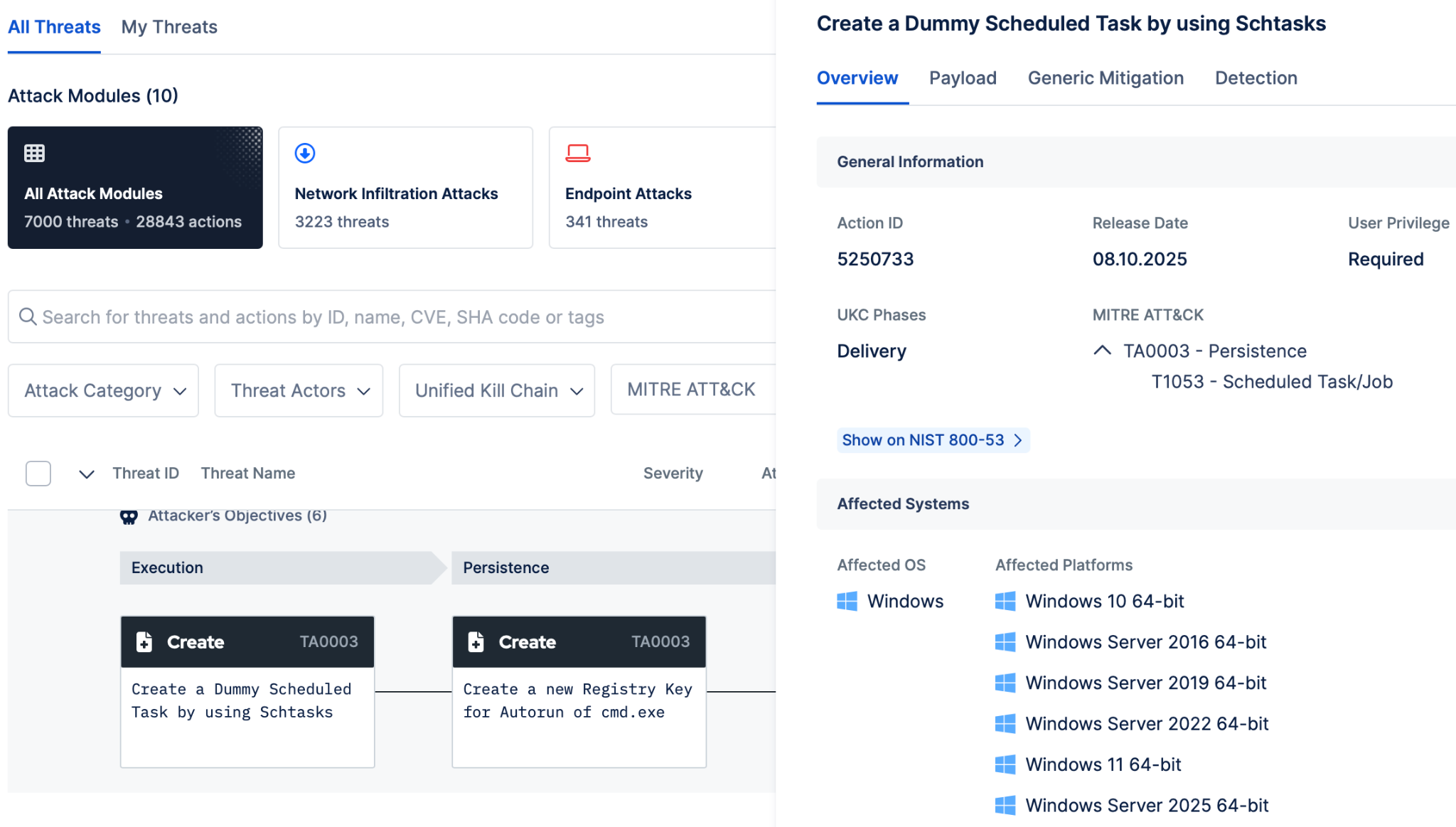
Fig. 1. MITRE ATT&CK Mapping of an Attack Simulation, Picus Security Control Validation (SCV)
For insurance purposes, ATT&CK-mapped BAS results do three things.
- They provide a measurable coverage baseline, not "we have strong endpoint protection" but "our EDR blocks 91% of tested credential access techniques and 60% of defense evasion techniques."
- They enable threat-specific assessment by demonstrating that your testing targets the exact technique chains used by active ransomware groups and the exfiltration methods driving current claims.
- And they create a defensible audit trail: quarterly ATT&CK heatmaps showing progressive coverage improvement give underwriters the continuous risk trending they now demand.
The practical value is straightforward: ATT&CK-mapped BAS results shift the underwriting conversation from "do you have security controls" to "here is how your controls perform against the specific techniques that drive the claims you are underwriting."
Why BAS and Automated Pentesting Answer Different Questions
Security vendors have stoked a debate about whether Breach and Attack Simulation (BAS) or Automated Penetration Testing (APT) is better, with some even explicitly arguing that automated pentesting should replace BAS entirely. While this debate sounds reasonable on the surface, it falls apart under operational scrutiny. For practitioners responsible for defending an organization, this framing is the problem.
It represents a coverage regression disguised as simplification.
Asking whether either BAS or automated pentesting alone is "enough" is like asking whether a smoke detector or a sprinkler system makes a building safer. They both perform fundamentally different functions, and neither, alone, is a "silver bullet".
Ultimately, BAS and automated pentesting answer fundamentally different security questions. Automated Penetration Testing takes a different, adversarial approach. It goes further by chaining vulnerabilities and misconfigurations together the way real attackers do. Automated pentesting asks a fundamentally different question: "How far could an attacker actually get?".
- Replacing BAS with automated pentesting would mean trading away continuous detection validation, control drift monitoring, and the ability to continuously test your entire defensive stack in exchange for deeper but periodic attack path insight.
- In this scenario, you’d gain adversarial depth, but lose defensive visibility. An organization running automated pentesting and no BAS equivalent knows what paths attackers can take, but it doesn't know whether its defenses would catch the attacker taking those paths. That's not a comprehensive security posture; that's half of a validation program.
Furthermore, some vendors market a clean run with zero findings as proof of protection, but it isn't. It simply means no exploitable path was found from that entry point, within that scope, at that moment. Your firewall, your SIEM rules, and your EDR logic all remain unvalidated. A no-finding pentest isn't a green light, it's a gap in visibility dressed up as confidence.
|
To present a complete, evidence-based profile to your cyber insurance carrier, you need both perspectives. Think of BAS as a series of independent measurements: does this control hold?. Does that gateway block, if not, detect, and alert?. Automated penetration testing is directional: it starts somewhere in your environment and moves, chaining whatever it finds into a path toward your most critical assets. One tells you how strong your controls are. The other tells you how far an attacker can get despite them. |
You Need Both: Offensive Depth and Defensive Breadth
The theoretical debate between BAS and Automated Pentesting fades when you look at actual production data. Real-world numbers clearly illustrate why underwriters want to see evidence from both: they reveal completely different halves of the same risk.
According to the Picus Red Report 2026, encryption-based attacks have declined by 38% year-over-year. Adversaries are pivoting to stealth, exfiltrating data through trusted application layer protocols and legitimate APIs. Attackers are avoiding your controls by blending in.
- The BAS Perspective (Defenses failing quietly): According to the Blue Report 2025, continuous simulation reveals that only 14% of logged adversarial activity actually generates an alert. Data exfiltration prevention succeeds just 3% of the time, and credential-based access succeeds in 98% of tested environments.
- The Automated Pentesting Perspective (Open doors): While BAS highlights the gaps in the fence, automated pentesting shows how easily an attacker can walk through them. With credential access succeeding 98% of the time, Automated Penetration Testing data shows the consequence: 22% of organizations have an open, unvalidated attack path straight to Domain Admin.
BAS shows you why the attacker isn't being caught; automated pentesting shows you where they will inevitably end up once they slip past your controls. Neither picture is complete without the other.

Translating BAS Findings into Cyber Insurance-Ready Risk Reports
So, you deploy both BAS and automated pentesting. You now have the offensive depth of Automated Penetration Testing and the defensive evidence of BAS. Is the job done?
Not quite. By running both, alongside your traditional vulnerability scanners, you have introduced a new operational nightmare: The Normalization Gap.
You now have a digital tsunami of disconnected finding streams flooding your team:
- Dozens of validated exploits from your Automated Penetration Testing solution.
- Continuous control gaps and detection failures from your BAS solution.
- Tens of thousands of theoretical vulnerabilities (CVEs) from your scanners.
Without an additional layer to merge, deduplicate, and prioritize these outputs, your remediation queue becomes unmanageable. A vulnerability marked "Critical" by a scanner is a much lower priority if your BAS platform has already proven that your WAF successfully blocks its exploitation. But if these tools operate in silos, you are forced to rely on CVSS-based guesswork, wasting time on theoretical risks while exploitable paths remain open.
How to Build a Continuous Evidence Package for Cyber Insurance Underwriting
You should never be forced to choose between Breach and Attack Simulation and Automated Penetration Testing.
Vendors pushing a "replace BAS" narrative are selling a false dichotomy that leaves your organization dangerously exposed and completely unprepared for modern cyber insurance underwriting.
If you choose only Automated Pentesting, you know your attack paths but have no idea if your firewalls, EDR, or SIEM will actually catch the intruder. If you choose only BAS, you know your controls work against known threats but might miss how a real attacker could chain a misconfigured permission and an unpatched service to reach your domain controller.
You absolutely need both. You need the offensive depth of Automated Pentesting to map the route, and the defensive breadth of BAS to prove your controls can block it. But running both tools in silos leads to operational chaos.
Picus Security Validation Platform for Supporting Cyber Insurance Underwriting
This is exactly where the Picus Security Validation Platform bridges the divide, turning disconnected alerts into the evidence-based reality underwriters require:
- BAS as the Foundation of Truth: At its core, the platform runs Picus Security Control Validation (SCV) module, a continuous BAS engine that continuously measures exactly how well your prevention and detection layers respond to known adversarial behaviors, all mapped to the MITRE ATT&CK framework. This establishes your baseline of defensive reality and provides the ultimate proof of due care for your insurers.
- The Unifying Intelligence Layer: The platform automatically ingests the attack paths found by your external Automated Pentesting tools, alongside the theoretical CVEs from your vulnerability scanners. Instead of treating these as isolated alerts, it places them directly alongside your continuous BAS data.
- Contextual Normalization: It then runs that combined dataset directly against your live BAS security control performance data. By unifying these dimensions, the platform eliminates theoretical noise. It transforms 50,000 disconnected findings into a single, deduplicated, and ranked action queue based strictly on confirmed, real-world exploitability.
- The Auditable Evidence Trail: For every validated finding, Picus delivers vendor-specific remediation guidance through its Picus Mitigation Library. After your team applies the fix, the BAS engine automatically re-validates, confirming the gap is closed. That closed-loop cycle, simulate, find, fix, verify, creates the exact documented evidence trail that modern underwriters demand.
Relying on just one tool leaves you with half a validation program, exposing you to claim denials and premium hikes. Relying on both without a coordinating platform leads to an unmanageable backlog.
To secure your cyber insurance in 2026, you must stop treating BAS and Automated Pentesting as an "either/or" decision. You need both offensive depth and defensive breadth, anchored firmly in the continuous evidence of BAS, and unified by a platform that turns disconnected data into a single, defensible source of truth.
Stop guessing and start proving your security. Request a free demo to see how unifying BAS and Automated Pentesting gives you the exact empirical evidence cyber insurers demand.




.png?width=353&height=200&name=picus-cyber-fundamentals-BAS-ROI-CISOs-preview-march5%20(1).png)


.png?width=353&height=200&name=picus-cyber-fundamentals-BAS%20Services%20Explainedpreview-feb23%20(1).png)

.png?width=353&height=200&name=G2-DEC-badge-update-preview%20(1).png)