Integrating BAS into Zero Trust Architecture (ZTA) for Validation
| March 27, 2026
TL:DR;
- BAS is the validation layer of Zero Trust, continuously proving that security controls actually prevent, detect, and respond to real-world attacker behavior.
- Zero Trust fails without control validation, as misconfigurations, policy drift, and detection gaps silently break defenses despite correct design.
- This guide provides a full integration architecture, showing how BAS connects with SIEM, EDR/XDR, and segmented environments to validate controls across trust boundaries.
- BAS validates behavior, not just configuration, testing microsegmentation, least privilege enforcement, and detection logic against real adversary techniques.
- Continuous BAS-driven feedback loops transform Zero Trust, enabling teams to detect gaps, apply mitigations, and re-validate defenses in an ongoing cycle.
Introduction: Why Breach and Attack Simulation (BAS) Is Essential for Zero Trust Architecture
Breach and Attack Simulation (BAS) tools strengthen Zero Trust Architecture (ZTA) by continuously validating that security controls actually prevent, detect, and respond to real-world attacker techniques.
Zero Trust assumes “never trust, always verify,” but most organizations only verify access, not whether their controls work under attack. Misconfigurations, policy drift, and detection gaps can silently break Zero Trust without visibility.
BAS closes this gap by simulating adversary behavior across your security stack, firewalls, EDR, SIEM, and segmentation controls, providing measurable evidence of control effectiveness and exposing failures before attackers do.
The Security Control Validation Gap in Zero Trust Deployments
Zero trust rests on several foundational principles:
- least privilege access,
- microsegmentation,
- continuous authentication, and an
- attacker-centric mindset.
Each of these principles depends on dozens of interconnected security controls, identity providers enforcing MFA, firewalls segmenting traffic between microservices, EDR solutions monitoring endpoint behavior, and SIEM platforms correlating anomalous events.
The challenge is that deploying these controls does not guarantee they work as intended.
- Firewalls drift from their intended rulesets.
- EDR agents miss detection signatures after updates.
- SIEM correlation rules fail to trigger alerts on novel attack chains.
- IPS may not be well moved and reconfigured after a DataCenter Architectural change
Misconfiguration alone accounts for a significant share of breaches, and these misconfigurations are invisible until an attacker, or a simulation, exposes them.
Traditional validation methods such as annual penetration tests offer only a point-in-time snapshot. By the time the report is delivered, infrastructure has changed, new applications have been deployed, and the threat landscape has shifted.
Zero trust requires something fundamentally different: continuous, automated validation that mirrors the pace of modern adversaries.
What Breach and Attack Simulation (BAS) Brings to a Zero Trust Tech Stack
Breach and Attack Simulation (BAS) platforms address the gap discussed earlier by safely simulating known adversary tactics, techniques, and procedures (TTPs) against your production security controls.
- Though BAS tools can perform CVE-based exploitation attacks, they do not walk attack paths the way an automated penetration testing tool would.
- Instead, BAS tests whether the prevention and detection layers you have deployed, firewalls, WAF, IPS, EDR, SIEM rules, email gateways, DLP, actually block and alert on known threat behaviors spanning the full range of the kill chain.
It answers a fundamentally defensive question: do your controls work as intended against the techniques real attackers use?
When integrated into a zero-trust architecture, BAS delivers several critical capabilities.
Continuous Security Control Validation
BAS assessments validate the effectiveness of the implemented preventive and detective measures by testing them against the known attack techniques observed in the wild.
Instead of assuming the effectiveness of a firewall rule, BAS will attempt to move simulated malicious traffic through that exact control point and report whether it was stopped, if not, detected, or missed entirely.
This aligns with the zero-trust concept of verifying every access request or data flow rather than assuming them.
Which Security Controls Can You Test with a BAS Solution?
Some, but not all, of the security controls that can be validated against known adversarial behavior observed in the wild are as follows.
|
Category |
Examples of Security Controls Validated by BAS |
|
Detection and Monitoring |
Security Information and Event Management (SIEM), Intrusion Detection Systems (IDS), Network Detection and Response (NDR) |
|
Network and Perimeter Security |
Next-Generation Firewalls (NGFW), Intrusion Prevention Systems (IPS), Web Application Firewalls (WAF), Secure Web Gateways (SWG) |
|
Email Security |
Secure Email Gateways (SEG) |
|
Endpoint Security |
Endpoint Protection Platforms (EPP), Endpoint Detection and Response (EDR), Extended Detection and Response (XDR), Anti-Virus (AV) & Anti-Malware (AM) Solutions |
|
Data Protection |
Data Loss Prevention (DLP) |
|
URL Filtering |
URL Filtering Solutions |
Microsegmentation Testing
One of the strongest features of zero trust is microsegmentation, or splitting the network into separate segments in such a way that an intrusion in one network segment does not spread quickly. However, implementing segmentation policies is not the same as ensuring that these policies are effective.
BAS assessments verify whether the controls in place for implementing segmentation policies, such as firewalls between VLANs, IPS policies governing east-west traffic, EDR detection logic for lateral movement techniques like pass-the-hash or SMB relay, actually block and alert on those behaviors.
BAS answers whether your defenses catch lateral movement attempts (behavior testing), not whether the path itself exists. Mapping the actual exploitable paths across segments, proving that an attacker can traverse from a compromised workstation to a database server in another zone, is the domain of Automated Penetration Testing (APT) solutions.
Full microsegmentation assurance requires both:
- BAS confirming controls detect and prevent known lateral movement techniques, and
- Automated Pentesting confirming no exploitable routes bypass those controls entirely.
Least Privilege Enforcement Verification
Zero Trust mandates that every user, workload, and device operates with the minimum level of access required, and that any attempt to exceed that boundary is detected and stopped. However, defining least privilege policies through RBAC and ABAC configurations is not the same as confirming those policies are enforced under real adversarial conditions.
BAS validates whether your prevention and detection controls, EDR, SIEM, endpoint policies, actually fire when privilege escalation behaviors are simulated against your environment. Rather than assuming an EDR policy catches token manipulation or credential abuse, BAS will simulate those exact techniques as observed in real malware and APT campaigns, and report whether the behavior was blocked, alerted on, or missed entirely.
BAS answers whether your controls detect and respond to privilege escalation attempts (behavioral testing), not whether a privilege boundary can actually be broken through a chained exploit sequence. Confirming that an attacker can move from a low-privilege account to domain admin by exploiting a specific vulnerability or misconfiguration chain is the domain of Automated Penetration Testing (APT) solutions.
Full least privilege assurance requires both:
- BAS confirming controls detect and prevent known privilege escalation techniques, and
- Automated Pentesting confirming no exploitable path exists that bypasses those privilege boundaries entirely.
Mapping BAS to MITRE ATT&CK Within Zero Trust
Each of the capabilities described above produces findings. But findings only drive Zero Trust investment decisions when they are expressed in a common language. MITRE ATT&CK provides that language.
The MITRE ATT&CK Matrix for Enterprise v18.1 consists of 14 tactics, 216 techniques, and 475 sub-techniques, cataloging the full spectrum of known adversary behavior.
- Modern BAS platforms map every simulation directly to ATT&CK techniques, which allows security teams to measure detection and prevention coverage as a percentage of relevant tactics.
- More importantly, this mapping reveals which stages of the kill chain have adequate coverage and which have gaps, critical intelligence for prioritizing zero trust investments.
For example, an organization might discover through BAS testing that its controls effectively detect initial access techniques (1190 exploit public-facing application) but fail to detect defense evasion (T1027 obfuscated files, T1055 process injection) and credential access (T1003 OS credential dumping). This tells the security team exactly where their zero trust architecture is weakest and where to focus hardening efforts.
This framework-aligned approach also supports compliance. Regulatory standards such as PCI DSS, SOX, NIST CSF & NIST SP 800 series, and ISO 27001 increasingly expect organizations to demonstrate active validation of their security controls, not just that they are deployed, but that they function as intended against realistic threats.
Breach and Attack Simulation (BAS) Integration Architecture for Zero Trust Environments
TL:DR;
- BAS agent placement must follow security policy boundaries, not network segments, ensuring accurate validation of controls per zone.
- Each Layer 7 security policy zone requires its own BAS agent if enforcement policies differ across segments.
- Single-agent deployments create misleading results when applied across heterogeneous security environments.
- Agent placement should reflect real-world enforcement differences across on-prem, cloud, branch, and remote environments.
- BAS requires outbound connectivity (HTTP/HTTPS), making deployment constraints critical in air-gapped or OT environments.
- SIEM and EDR/XDR integration is API-driven, validating whether simulated attacks generate expected logs and alerts.
- Detection failures fall into four categories: unlogged, logged but not alerted, delayed alerts, and blocked but unlogged.
- “Blocked but unlogged” events are critical blind spots, indicating logging and visibility gaps rather than successful defense.
- BAS validates identity-layer attacks indirectly via SIEM/EDR, not through direct integration with IdPs or PAM solutions.
- Effective Zero Trust validation requires correct deployment architecture, including agent placement, integration design, and environment-specific constraints.
Agent Deployment Across Trust Boundaries
BAS agents should be placed in each distinct Layer 7 security policy zone, not simply in every microsegment at the network level.
The operative question is: do any two segments operate under different IPS, AV, or application-layer inspection policies? If yes, each policy zone requires its own agent to independently validate the controls enforced on that traffic path.
Deploying a single agent and extrapolating results across policy-heterogeneous segments is a methodology error that will produce misleading coverage metrics.
Practical placement targets include:
- On-premises LAN segments with distinct NGFW/IPS policy profiles
- Cloud VPCs and landing zones where cloud-native WAF, CWPP, and security group rules differ from on-premises enforcement
- Branch offices where reduced-stack configurations may create undetected policy drift versus HQ environments
- Remote worker endpoints enrolled in conditional-access and split-tunnel VPN policies
|
A critical constraint to understand. BAS agents execute simulations by downloading threat payloads from a dedicated content delivery domain over HTTP (TCP 80) and HTTPS (TCP 443). This means agent placement is only viable where outbound internet access, or an on-premises mirror of the threat content server, is architecturally feasible. OT/ICS and air-gapped IoT network segments are fundamentally incompatible with this operational model unless the BAS platform offers a full on-premises deployment mode with a locally hosted file server. Architects should not assume BAS agent parity across IT/OT boundaries without verifying this capability explicitly. |
For read-only or resource-constrained environments (e.g., branch offices, DMZ nodes), many BAS platforms offer a lightweight browser-based agent that requires no installation, supports on-demand validation of HTTP/HTTPS threat downloads without a persistent service footprint, and can be removed immediately post-assessment.
SIEM and EDR/XDR Integration
Modern BAS platforms are expected to integrate with security analytics infrastructure, specifically SIEM, EDR, and XDR, through a dedicated Integration Agent that queries those platforms via API after a simulation run completes. This is an active query-pull model, not a passive log-push. The Integration Agent authenticates to the security platform using API credentials, queries the relevant log and alert data generated during the simulation window, and validates whether the expected detection events are present.
This architecture reveals four distinct failure classes that architects and SOC engineers should plan to investigate, not the commonly oversimplified binary of "log forwarding gap or missing detection rule":
|
Failure Class |
Observed Result |
Root Cause Categories |
|
Unlogged |
Threat simulated; no log entry found |
Missing log source, incorrect field mapping in the query, log agent not deployed, exporter misconfiguration |
|
Logged, not alerted |
Log ingested; no alert triggered |
Missing correlation rule, alert suppressed by tuning policy, threshold not met |
|
Alert delayed |
Alert present but arrives outside the query window |
Log pipeline latency, indexing delay, integration configuration requiring tuning |
|
Blocked, not logged |
Security control blocked the attack but generated no telemetry |
Control logging disabled, wrong severity threshold, parsing error producing malformed log fields |
Particularly important: blocked actions should still produce telemetry.
If a simulation confirms that a payload was blocked by an IPS or endpoint control but no corresponding log is found in the SIEM, the problem is almost certainly a logging configuration gap, not an indication that the control worked silently by design. These "blocked but unlogged" results are high-value operational findings because they represent blind spots in dwell-time detection and post-incident forensics.
Regarding SOAR integration: BAS-to-SOAR orchestration is an architectural pattern that organizations can design, but it is not a native capability built into most BAS integration frameworks. The BAS platform validates whether events were logged and alerted; downstream SOAR automation is a separate integration layer that consumes SIEM alerts. Architects should not assume out-of-the-box SOAR connectivity when evaluating BAS platforms, validate this explicitly against the vendor's API and webhook capabilities.
Credential-Based Attack Coverage and Identity-Layer Validation
BAS platforms can simulate a broad range of credential access and lateral movement techniques that are directly relevant to identity-layer controls in a zero trust architecture. These include, but are not limited to: LSASS memory dumping, credential extraction from the Windows Security Account Manager (SAM), Kerberoasting, AS-REP roasting, pass-the-hash, pass-the-ticket, DCSync, token impersonation, and privilege escalation via token manipulation.
However, it is architecturally incorrect to describe this as "integration with identity providers (IdPs) or privileged access management (PAM) solutions." That characterization conflates simulation capability with integration architecture. How this actually works:
- The BAS agent executes credential-access techniques on the endpoint using the configured service account and (optionally) a standard non-privileged user account, mirroring the dual-privilege execution model of real-world attackers.
- The endpoint security control (EDR/EPP) or SIEM with behavioral analytics is expected to detect the technique. Detection results are validated through the SIEM/EDR/XDR integration layer, not through a direct IdP or PAM query.
- If a credential attack such as LSASS dumping goes undetected in the SIEM, the remediation action is updating the detection rule or the EDR behavioral policy, not modifying an IdP or PAM configuration.
BAS platforms do not natively query IdP audit logs (e.g., Azure AD Sign-In Logs, Okta System Log) nor do they connect to PAM vaults (e.g., CyberArk, BeyondTrust) via API to validate session controls. If an organization wants to validate IdP-level detection of credential attacks, the correct integration path is: ingest IdP audit logs into the SIEM, then run BAS credential simulations, and validate detection through the existing SIEM integration. The IdP is an indirect data source via SIEM, not a direct integration target.
|
Architectural note on agent privilege. The accuracy of endpoint attack results depends significantly on how the BAS agent is configured. High-privilege techniques (e.g., LSA manipulation, PPL bypass, privilege token duplication) must be executed under an administrative service account. Techniques representative of a post-phishing, standard-user threat actor should be executed under a non-privileged user account. BAS platforms that support dual-user execution (privileged service account + optional standard user) produce more operationally representative results than single-account configurations. |
Deployment Models for Cloud and Hybrid Environments
Modern BAS platforms support multiple deployment architectures that have meaningfully different security and connectivity implications. Understanding these distinctions is essential for accurate zero trust validation:
SaaS (Cloud-Hosted) Deployment
The BAS management plane, threat content server, attack emitters, and reporting infrastructure all run in the cloud. Agents deployed in customer environments communicate outbound to the SaaS platform and download threat content from the cloud-hosted infrastructure using standard encrypted communication protocols. This model requires outbound internet access from every agent machine.
Hybrid Deployment
The Hybrid deployment model combines on-premises management with cloud-hosted attack infrastructure, giving organizations the operational control of a local deployment without the full infrastructure footprint of a completely self-hosted solution.
This model is well-suited for organizations that have data residency or compliance requirements around management and configuration data, while still maintaining connectivity to the internet. Security and data isolation principles are maintained throughout, and sensitive customer data remains within the customer's environment.
Full On-Premises Deployment
All components, manager, database, analytics, and attack emitters, run within the customer environment. This model is designed for organizations with strict data residency requirements, air-gapped networks, or regulatory constraints that prohibit outbound cloud dependencies. Threat content and attack emitters are served locally, and the platform maintains internal synchronization mechanisms to keep attack content current. Some attack modules may have specific connectivity considerations depending on the organization's infrastructure configuration, which should be validated during the deployment scoping phase with the vendor.
Architectural Implication for Zero Trust Validation
BAS does not "cross cloud-to-on-prem boundaries" by executing attacks that transit from cloud to on-prem infrastructure on behalf of the attacker, agents must still be placed locally within each network segment to be validated.
The platform architecture determines where management and emitter infrastructure reside; agent placement determines what security controls are tested. A hybrid deployment does not substitute for placing agents in each policy-distinct zone. The control validation happens at the egress point from the agent's segment, not at a cloud/on-prem transition point in the abstract.
For each deployment model, connectivity requirements between agent machines and the platform's attack content infrastructure must be confirmed as part of the deployment planning process. Deployment-specific connectivity requirements are addressed during the implementation scoping phase with the vendor.
Benefits of Integrating BAS into Zero-Trust Architecture
One of the most valuable aspects of integrating BAS into zero trust is the creation of a continuous feedback loop.
The process follows a repeatable cycle:
- First, your selected BAS platform executes a comprehensive simulation aligned to your threat profile, the adversary groups, TTPs, and attack vectors most relevant to your industry and geography (all based on a comprehensive threat library).
- Second, the platform analyzes results and generates prevention and detection scores for each control tested, mapping failures to specific ATT&CK techniques.
- Third, security teams receive actionable remediation guidance from its mitigation library, both vendor-specific & vendor-neutral recommendations such as exact firewall rules, SIEM correlation queries, or EDR detection signatures to deploy.
- Fourth, after remediating identified gaps, the team reruns simulations to verify that fixes are effective. This cycle repeats continuously.
This feedback loop is what transforms zero trust from a static policy framework into a living, adaptive security posture. It accounts for the reality that environments change constantly, new cloud workloads are provisioned, developers push application updates, employees onboard and offboard, and adversaries evolve their tradecraft.
Without continuous validation, zero trust controls degrade silently over time.
Deploying BAS within a zero trust architecture involves several key integration points that security architects should plan for.
Choosing the Best BAS Platform for Zero Trust Architecture (ZTA) Validation
When evaluating BAS tools specifically for zero trust support, security teams should prioritize several technical and operational criteria.
- First, the platform’s threat library must be continuously updated, ideally with rapid turnaround times for emerging threats.
Modern adversaries evolve daily, and validation platforms must keep pace. Leading solutions differentiate here by delivering near real-time threat intelligence integration and ready-to-run attack scenarios that reflect active campaigns observed in the wild.
- Second, MITRE ATT&CK alignment should be native and comprehensive, covering the full attack lifecycle from initial access to impact.
This ensures that validation results are expressed in a standardized language that both technical teams and executives can act on.
- Third, organizations should look for true continuous and automated validation, not periodic testing.
BAS platforms are most effective when they operate as part of a continuous validation loop, enabling organizations to detect control drift, misconfigurations, and detection gaps as they emerge, not months later. This continuous approach is a core requirement for modern exposure management and CTEM programs.
- Fourth, depth of security control validation matters.
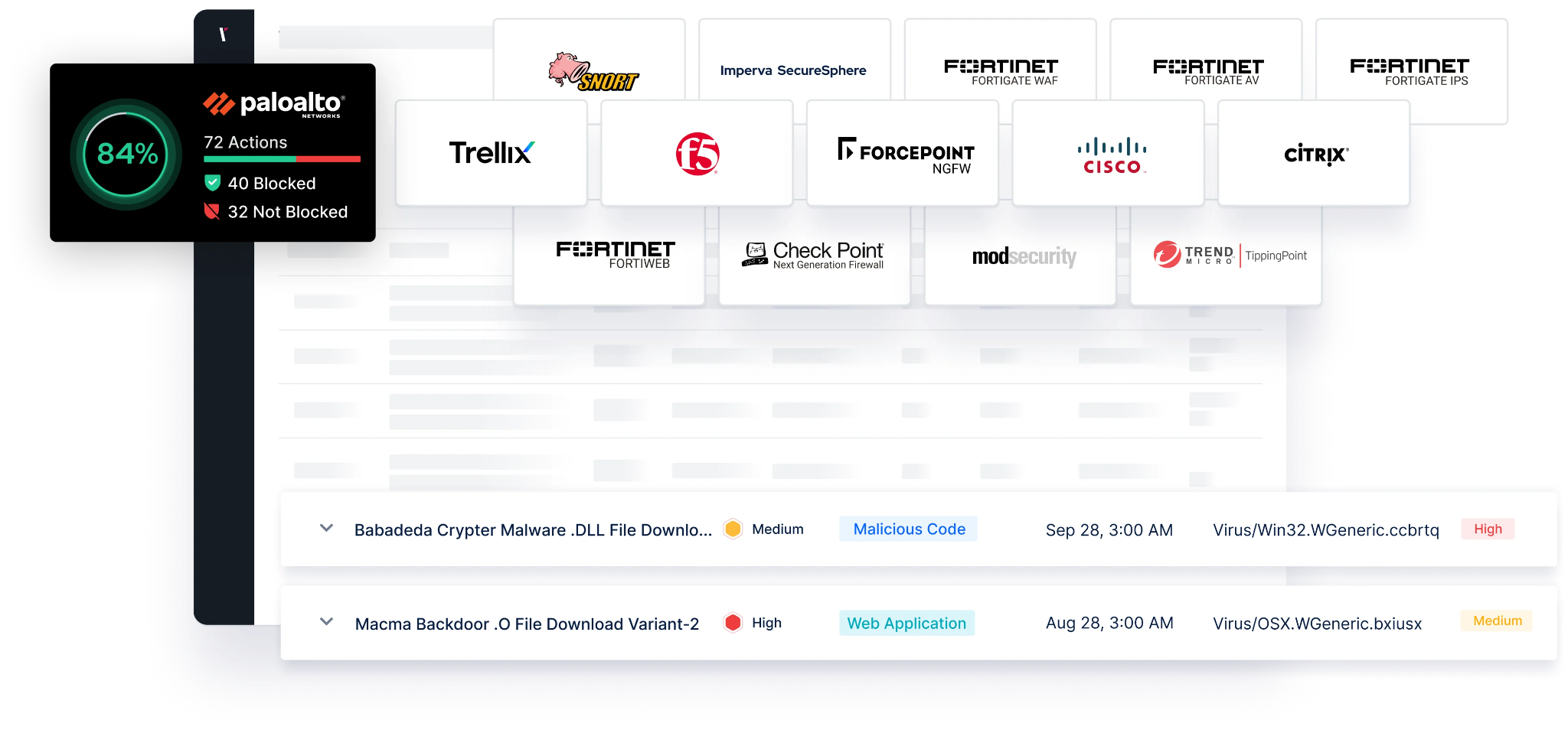
A mature BAS solution should validate both prevention and detection layers across the entire security stack, firewalls, EDR, SIEM, email security, and data protection controls, providing clear evidence of whether controls actually stop or detect real-world attack techniques.
Fifth, actionable mitigation is non-negotiable. Identifying gaps is only the first step; the platform must provide validated, vendor-specific and vendor-neutral remediation guidance. Advanced BAS platforms go further by pre-validating mitigation content (such as SIEM rules or IPS signatures), enabling security teams to close gaps quickly and confidently rather than experimenting blindly.
Picus Security Control Validation as the Best Breach and Attack Simulation (BAS) Solution
This is where leading platforms like Picus Security Control Validation stand out in practice. Rather than stopping at gap identification, Picus combines:
- A continuously updated threat library powered by dedicated threat research teams
- Ready-to-run attack simulations aligned with real-world campaigns
- Deep and versatile integrations of security controls,
- Validated mitigation guidance across multiple vendors,
- And closed-loop validation, allowing teams to immediately verify whether fixes actually work
This approach reflects a broader industry shift: from discovering exposures to proving and improving security effectiveness through continuous validation.
Finally, ease of deployment and integration should not be overlooked. The best BAS platforms integrate seamlessly into existing environments (SIEM, EDR, ticketing systems) and support hybrid, cloud, and on-premises architectures without introducing operational friction.
Validate every layer of your zero trust architecture with real adversary behavior.
Request a free demo and see exactly where your controls fail, detect, or stop attacks.





.png?width=353&height=200&name=picus-cyber-fundamentals-BAS-ROI-CISOs-preview-march5%20(1).png)


.png?width=353&height=200&name=picus-cyber-fundamentals-BAS%20Services%20Explainedpreview-feb23%20(1).png)
